Every business owner we speak with is asking about AI. And fair enough—the potential is real.
But here’s what we’re seeing: most SMEs are diving into AI tools without checking whether they’re actually ready to get value from them.
The good news? You don’t need a comprehensive AI strategy or a transformation roadmap. Most organisations are finding their way with AI one step at a time—trying Copilot here, experimenting with automation there, learning as they go.
But there are three fundamental questions that determine whether those experiments will succeed or flounder. Get these Copilot readiness fundamentals right, and you’re set up to learn and adapt. Get them wrong, and you’ll waste time and money on AI tools that don’t deliver.
Question 1: Is Your Organisational Data AI-Ready?
This is the foundation everything else is built on. AI is only as good as the data it can access and understand. Yet this is where we see the biggest gap between expectation and reality.
Ask yourself three things:
Is your data accessible? If your critical business information lives in local drives, personal folders, or filing cabinets, AI can’t help you. For AI to be useful, your data needs to be in connected systems—SharePoint, OneDrive, your line-of-business applications. Not everything needs to be perfect, but the information your team actually uses daily should be digitally accessible. (Learn how SharePoint can transform your information management.)
Is your data current and clean? Most organisations have years of digital clutter. Old versions of documents. Outdated information no one’s touched since 2015. Duplicate files scattered across different locations. When AI tools search through that mess, they can’t tell what’s current and what’s obsolete. You don’t need to clean everything overnight, but you do need to know where your source of truth sits for important information.
Is your data properly governed? Here’s the kicker: AI respects the same permissions your people do. If your SharePoint permissions are a mess—where anyone can access anything, or critical information is locked down so tightly that no one can find it—those same problems will plague your AI tools like Copilot. Good AI outcomes require good information governance.
Good information governance means having clear ownership of information, consistent permission structures, and documented policies about who should access what. For example, your finance team should be able to access budget documents while keeping them restricted from general staff—and those same boundaries will guide what Copilot can surface for different users.
The reality check: If someone new joined your team today, could they find the information they need within your digital environment? If the answer is “not really,” then AI won’t fare much better.
Once your data foundation is solid, the next question is whether your technology environment can support safe experimentation.
Question 2: Is Your Technology Foundation Ready for Safe Experimentation?
You don’t need cutting-edge infrastructure to benefit from AI. But you do need an environment that’s stable and secure enough to turn on AI features without creating new risks. Copilot readiness starts with your technology foundation.
Is your Microsoft 365 environment in good shape? For most SMEs, AI adoption starts with the Microsoft ecosystem—Copilot in Word, Teams, Outlook. But if your M365 environment has security gaps, inconsistent configurations, or systems that don’t talk to each other properly, you’re building on shaky ground. Basic hygiene matters: multi-factor authentication, proper licensing, security policies that actually work.
(For detailed guidance: Discover which M365 security features you should be using to protect your Copilot deployment)
Can you pilot safely? The beauty of modern AI tools is that you can test small before committing big. But that requires an environment where you can trial features with a subset of users, measure what happens, and roll back if needed. If your systems are so fragile that any change creates chaos, you can’t learn effectively.
Do you have the right guardrails? AI amplifies everything—including security risks. Before you enable AI tools like Copilot across your organisation, you need basic data protection and compliance frameworks in place. Not perfect, just appropriate for your business. What information can AI tools access? What can they do with it? Who’s responsible for monitoring usage?
The goal isn’t perfection. It’s having a solid enough foundation that you can experiment, learn, and scale what works without creating new problems.
With your data and technology foundation in place, success ultimately depends on whether your people can actually use these tools effectively.
Question 3: Can Your People Actually Adopt and Iterate with AI?
Technology is only half the equation. The other half is whether your team can realistically learn, use, and benefit from AI tools.
Do people have time and permission to experiment? Here’s what doesn’t work: rolling out Copilot or other AI tools and expecting people to figure them out on top of their already-full workload. Successful AI adoption requires some dedicated time for learning, testing, and adjusting workflows. Not months—but enough space to properly onboard.
Are expectations realistic? AI isn’t magic. It won’t solve problems that are actually people or process issues. It won’t replace thinking. And it definitely won’t deliver value overnight. Teams need to understand what AI can genuinely help with (automating repetitive tasks, surfacing information faster, drafting routine content) versus what it can’t (strategic thinking, relationship building, complex decision-making).
Is there a culture of learning? The organisations getting value from AI are the ones that treat it as an ongoing learning process, not a one-and-done implementation. That means being comfortable with trial and error. Sharing what works and what doesn’t. Adjusting approach based on real experience. If your culture punishes mistakes or resists change, AI adoption will be an uphill battle.
Can you build capability over time? You don’t need everyone to become an AI expert. But you do need some internal capability to assess tools, guide usage, and help people improve their skills progressively over time. Whether that’s upskilling existing staff or bringing in external support, there needs to be a path for building competence.
And remember: not everyone will embrace AI at the same pace. Some team members will dive in immediately while others need more time and support. Both approaches are valid.
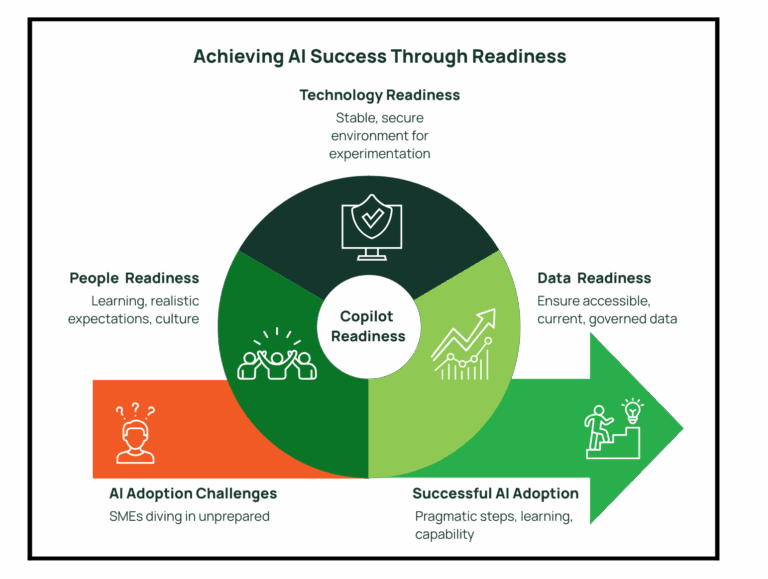
What This Means for You
If you’re reading these three questions and thinking “we’ve got some work to do”—that’s completely normal. Very few SMEs tick all these boxes today.
The key is knowing where you stand so you can make informed decisions about where to invest your time and budget. Maybe you need to clean up your data environment before deploying AI tools. Maybe your technology foundation is solid but your team needs more support. Maybe you’re actually in better shape than you thought and just need confidence to start experimenting.
AI readiness isn’t about having everything perfect. It’s about having the fundamentals right so you can explore opportunities as they emerge, learn from what works, and build capability over time.
That’s how successful AI adoption actually happens in the real world—one pragmatic step at a time.
There’s a world of difference between Power BI dashboards that look impressive and ones that actually change how you run your business. The pretty ones get admired in meetings, but truly effective Power BI dashboard creation focuses on solutions that are regularly monitored because they genuinely influence what happens next.
The distinction matters more than you might think. Most business intelligence solutions fail not because the data is wrong or the charts are ugly, but because they don’t connect the dots between information and action. They tell you what happened, but they don’t help you decide what to do about it.
When Power BI Dashboards Actually Change Business Outcomes
The most powerful custom Power BI dashboards share a common trait: they answer the questions that keep business owners awake at 3am. Not the questions they think they should be asking, but the ones that genuinely matter for their specific situation.
Consider a manufacturing business struggling with cash flow despite strong sales figures. Traditional Excel reports might show revenue trends and expense categories, but effective Power BI dashboard creation focuses on what they really need to see—the gap between when they invoice clients and when payments actually hit the bank. Custom reporting solutions showing aging receivables alongside cash flow projections help spot potential shortfalls weeks in advance, enabling action before problems become crises.
That’s the difference between basic reporting and comprehensive business intelligence solutions. Reporting tells you that your receivables are $150,000. Well-designed dashboards tell you that based on current aging patterns; you’ll be $30,000 short of covering next month’s payroll unless you chase three specific overdue invoices this week.
The Psychology Behind Effective Power BI Dashboard Creation
Human beings are remarkably good at ignoring information that doesn’t lead to clear action. It’s not laziness—it’s cognitive efficiency. When faced with pages of charts and tables, most business managers will glance at the headlines and move on to something they can actually do something about.
This is why professional Power BI services focus ruthlessly on decision points rather than data points. Instead of showing every possible metric, effective data visualisation tools highlight specific information that should trigger specific responses. Revenue down 15% this month? Well-designed business intelligence solutions don’t just show the decline—they break down which products, customers, or regions are driving the drop, giving you somewhere concrete to start investigating.
The best custom Power BI dashboards also understand timing. There’s no point alerting someone to a problem they can’t solve until next week, but there’s enormous value in highlighting issues that need attention right now. This is where automated alerts and exception reporting become powerful—not because they eliminate human judgment, but because they focus it on the decisions that matter most.
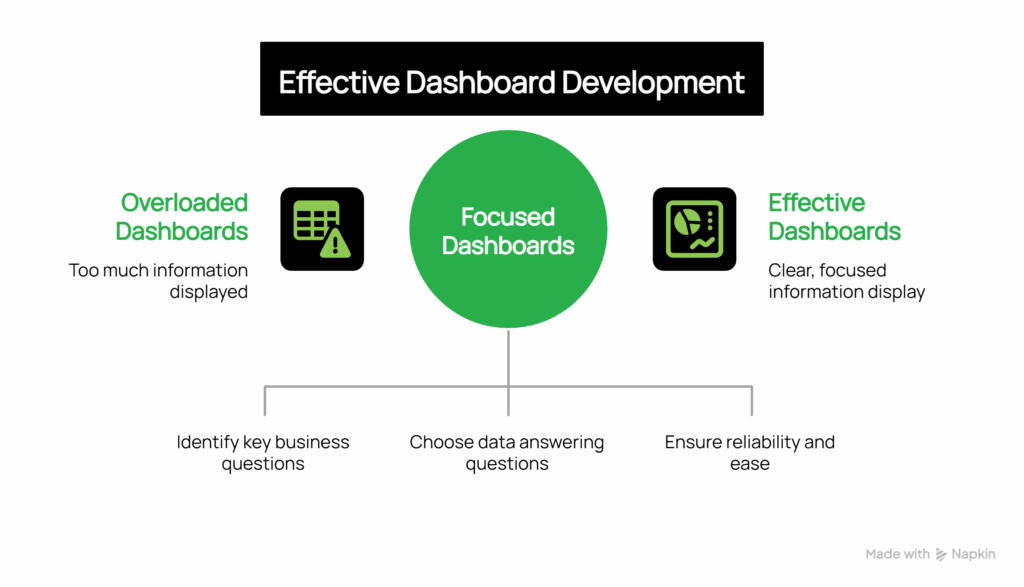
Beyond Pretty Charts: Professional Power BI Dashboard Creation
Visual appeal matters, but not for the reasons most people think. Well-designed reporting solutions aren’t effective because they look good—they’re effective because they make complex information instantly understandable. The goal isn’t to impress visitors in the boardroom; it’s to help busy managers make better decisions faster.
Effective Power BI dashboard creation follows the way people actually consume information under pressure. The most critical metrics need to be visible at a glance, ideally with clear indicators of whether things are tracking well or need attention. Detailed information should be available but not overwhelming—accessible through drilling down rather than cluttering the main view.
Context is everything in business intelligence solutions. Showing this month’s sales figure is interesting. Showing this month’s sales compared to target, last month, and the same month last year starts to tell a story. Adding trends, seasonal patterns, and leading indicators transforms data into insight.
Common Power BI Dashboard Mistakes That Kill Decision-Making
The most common mistake in dashboard development is trying to put everything on one screen. The “single pane of glass” approach sounds logical until you realise that different decisions require different information. A sales manager needs to see pipeline health and conversion rates. A CFO needs cash flow and profitability trends. An operations manager needs capacity utilisation and quality metrics. Custom solutions trying to serve all these needs end up serving none of them well.
Don’t fall into the trap of building data visualisation tools around the data you have rather than the decisions you need to make. Just because your CRM captures 47 different fields doesn’t mean they all belong on your sales dashboard. The most professional Power BI services start with an important business question—”Are we on track to hit our quarterly target?”—then work backwards to identify which specific data points help answer that question.
Technical complexity can also undermine effectiveness. Reporting solutions that take forever to load, require special training to interpret, or break every time someone updates the underlying data quickly become abandoned. The most successful business intelligence solutions prioritise reliability and simplicity over sophistication.
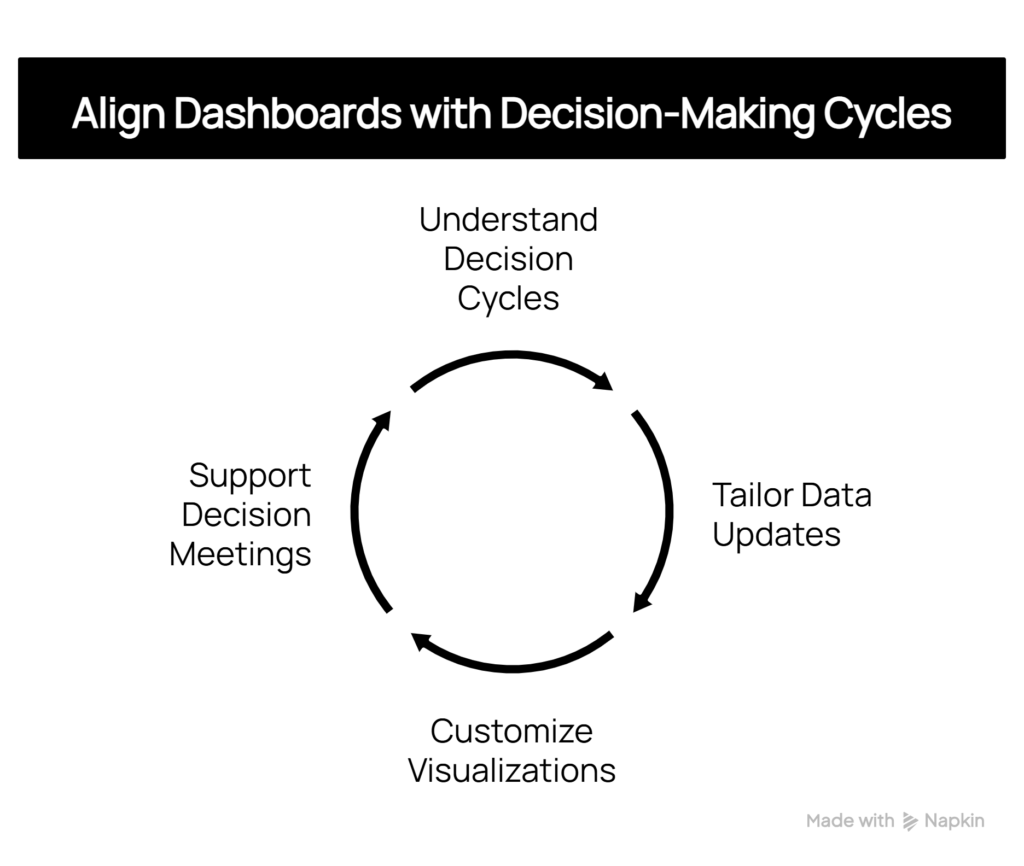
Aligning Power BI Dashboards with Your Decision-Making Cycles
Decision-making cycles vary across businesses, and effective dashboard development should reflect these patterns. A retail business might require daily inventory updates but only weekly sales trend analysis. A professional services firm might focus on monthly utilisation rates while needing real-time project status updates.
The key is understanding how and when decisions are made within your organisation. If your management team meets every Tuesday morning to review performance, your reporting solutions should support that cycle—with data that’s current as of Monday night and focused on issues that can be addressed in the coming week.
Likewise, individual managers need custom data visualisation tools that align with their daily workflow. A warehouse manager checking stock levels at 6am needs different information, presented differently, than a marketing director reviewing campaign performance during afternoon planning sessions.
The Strategic Impact of Business Intelligence Solutions
When Power BI dashboards are designed around decision-making rather than data display, they start to change how businesses operate. Managers become more proactive because they can spot trends early. Teams become more aligned because everyone’s looking at the same key metrics. Strategic planning becomes more grounded because it’s based on clear, current information rather than gut feel and outdated reports.
Perhaps most importantly, effective business intelligence solutions help businesses learn about themselves. Patterns emerge that weren’t visible in traditional reporting. Correlations become apparent between seemingly unrelated activities. Over time, this deeper understanding leads to better strategy and more confident decision-making.
The transformation isn’t just about having better information—it’s about developing a more systematic, evidence-based approach to running the business through professional Power BI dashboard creation.
Ready to explore how custom Power BI dashboards could transform decision-making in your business? Our consulting services specialise in creating intelligent solutions that connect data to action, helping Australian businesses make faster, better-informed decisions.
Every Australian business has at least one Excel spreadsheet that started innocently enough—a simple way to track something important. Fast forward twelve months, and that same spreadsheet has become a business-critical monster with multiple tabs, complex formulas, and three different people trying to update it simultaneously. When someone accidentally deletes a column or overwrites crucial data, the entire operation grinds to a halt.
This evolution from helpful tool to operational liability happens gradually, which is why many business owners don’t realise when Excel has outlived its usefulness. The moment you find yourself saying “don’t touch that spreadsheet—it runs the business,” it’s time to consider Power Apps Excel replacement solutions.
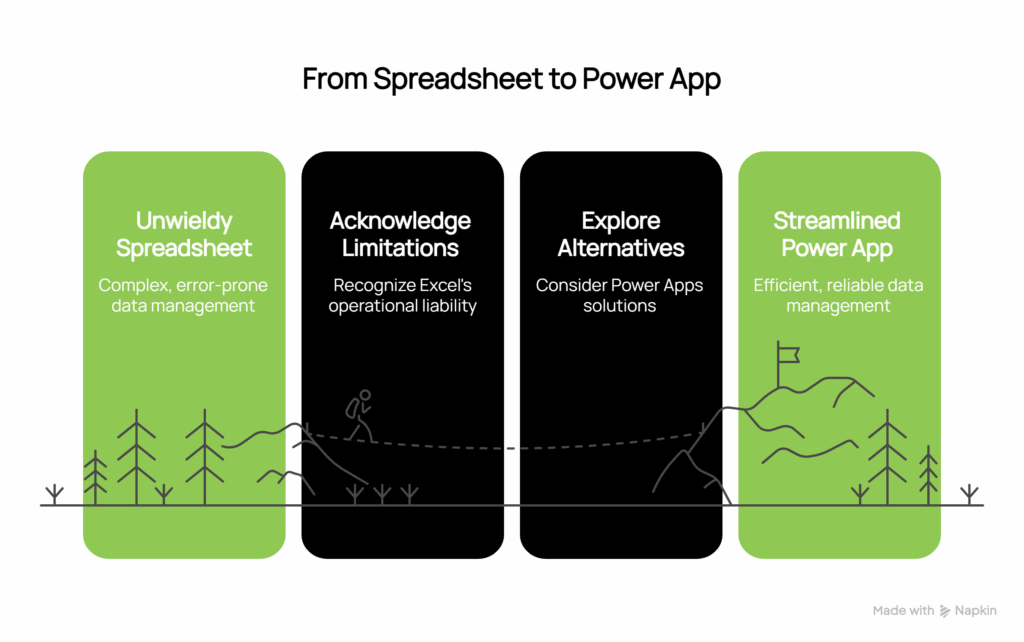
Why Australian Businesses Are Moving Beyond Excel
Excel performs exceptionally well at calculations and data analysis, but it becomes problematic when treated as a business application. The issues compound as your business grows and more people need access to critical information stored in shared spreadsheets.
Version control becomes chaotic when multiple copies float around with different data, making it impossible to know which version is correct. Data corruption risks escalate dramatically—one wrong click can destroy months of carefully maintained information with no easy recovery option. Access limitations prevent field staff from easily updating information from mobile devices, creating delays and data gaps that impact real-time decision making.
Manual process bottlenecks emerge when simple tasks like approvals require emailing spreadsheets back and forth through multiple people. Perhaps most concerning is the complete absence of audit trails—there’s no way to track who changed what information when, creating compliance and accountability issues that can expose your business to significant risk.
The solution isn’t to find better ways to manage Excel—it’s to replace Excel with purpose-built applications that handle multi-user business processes properly.
5 Simple Power Apps Every Business Needs
Employee Directory and Contact Management transforms that shared Excel file containing everyone’s contact details, emergency contacts, and skills information. A well-designed employee directory provides searchable interfaces, photo integration, and role-based access without the constant version conflicts that plague shared spreadsheets. Teams can quickly locate colleagues, understand reporting structures, and access essential contact information without navigating complex spreadsheet tabs.
Equipment and Asset Tracking converts your equipment maintenance spreadsheet into a mobile-friendly asset management system. Modern asset tracking incorporates barcode scanning, maintenance scheduling, and condition reporting that updates in real-time rather than waiting for someone to manually update Excel rows back at the office. Maintenance teams can log issues immediately, schedule preventive maintenance automatically, and generate reports that provide genuine insights into asset performance.
Leave Request and Approval Systems replace the holiday tracking spreadsheet that requires manual calendar updates and email chains for approvals. Automated workflow systems allow staff to submit requests through mobile apps, enable managers to approve with automatic notifications, and update calendars without manual intervention. This eliminates the confusion of overlapping leave requests and ensures adequate coverage planning.
Incident and Safety Reporting converts safety incident logs or customer complaint tracking from Excel into structured reporting systems. These applications include photo attachments, automatic notification workflows, and follow-up task creation that ensures nothing falls through the cracks. Management gains visibility into patterns and trends that might be hidden in spreadsheet rows, enabling proactive responses to emerging issues.
Expense Tracking and Approval ends the monthly ritual of collecting expense spreadsheets from different team members. Modern expense systems feature receipt photo capture, automatic approval routing based on amounts and categories, and direct integration with your accounting software. This streamlines reimbursement processes while providing better visibility into spending patterns and budget compliance.
The Business Case: Power Apps vs Excel for Business Management
When businesses transition from Excel to proper Power Apps solutions, the transformation goes beyond just replacing spreadsheets. These applications provide capabilities that Excel simply cannot match in multi-user business environments.
Real-time collaboration allows multiple users to update information simultaneously without conflicts or data corruption. Mobile accessibility ensures field staff and remote workers can access and update critical information from anywhere, supporting the flexible work arrangements that modern businesses require. Automated workflows handle approval processes, notifications, and task creation based on business rules, reducing administrative overhead while improving consistency.
Data integrity features include built-in validation that prevents common data entry errors and maintains consistency across all records. Comprehensive audit capabilities provide complete history tracking of who changed what information and when, supporting compliance requirements and accountability frameworks that are increasingly important in regulated industries.
Perhaps most importantly, these solutions scale with your business growth rather than becoming more problematic as you add users and complexity. While Excel becomes exponentially more difficult to manage with additional users and data volume, properly designed Power Apps maintain performance and usability regardless of scale.
Professional Power Apps Development Services
While the concept of replacing Excel spreadsheets with Power Apps might sound straightforward, proper implementation requires understanding of data architecture, user experience design, and business workflow optimisation. The difference between a basic app and one that truly transforms your operations lies in the details of how information flows between systems and users.
Professional development services ensure that your new applications integrate seamlessly with existing business systems, provide intuitive user experiences that encourage adoption, and include the robust error handling and security measures that business-critical applications require. The technical complexity of building reliable, scalable business applications means that while the end result appears simple, the underlying development requires expertise in database design, user interface optimisation, and business process automation.
The investment in professional development pays dividends through reduced training requirements, higher user adoption rates, and applications that continue to serve your business effectively as requirements evolve. Rather than creating another system that becomes problematic over time, proper planning and implementation create foundations that support long-term business growth.
Ready to replace problematic Excel spreadsheets with professional Power Apps solutions? Our Power Apps development services specialise in creating simple, powerful business applications that eliminate spreadsheet chaos while integrating seamlessly with your existing systems.
Running a nonprofit means juggling countless priorities with limited resources. Every minute spent on administrative tasks is time that could be advancing your cause.
Microsoft Copilot offers nonprofit organisations a practical solution to streamline communications while maintaining the personal touch that makes your work meaningful.
Here are five strategies to help your nonprofit leverage Copilot effectively, with ready-to-use examples that deliver results.
1. Transform Your Donor Communications
Strong donor relationships are built on consistent, thoughtful communication. Copilot helps you craft personalised messages that honour your supporters’ contributions while maintaining your organisation’s authentic voice.
Why Copilot improves donor communications: Copilot eliminates the time-consuming process of starting from scratch with each thank-you note while ensuring consistent messaging that reflects your organisation’s voice. It helps you include specific program details you might otherwise forget in routine communications, enabling personalisation at scale without sacrificing quality.
Try this approach: “Write a thank-you letter for a $500 donor to our literacy program. Include specific details about how their gift helps children learn to read and mention our recent milestone of reaching 200 students this year.”
This ensures every donor feels valued and understands their impact, strengthening long-term partnerships that sustain your mission.
2. Build Your Volunteer Community More Effectively
Finding volunteers who truly connect with your cause requires clear, compelling communication about opportunities and impact. Copilot can help you create recruitment materials that attract the right people.
Why Copilot improves volunteer recruitment: Copilot helps you craft descriptions that clearly communicate both the practical details volunteers need (time, tasks, impact) and the emotional connection that motivates them to commit long-term. It ensures you don’t undersell the opportunity or overwhelm with unnecessary details, creating communications that attract volunteers who are genuinely aligned with your mission.
Here’s how: “Create a volunteer opportunity description for our food bank sorting shift. Emphasise the community impact, time commitment (3 hours monthly), and how volunteers directly help families access nutritious meals. Lead this opportunity with the impact ‘Help XX number of families get access to nutritious meals over a 3-hr volunteer shift'”
3. Strengthen Your Fundraising Stories
Successful fundraising combines data with heart. Copilot can help you weave together compelling narratives that show both the need for support, and the tangible outcomes donors make possible.
Why Copilot improves fundraising appeals: Copilot excels at weaving statistics into compelling narratives, helping you avoid the common pitfall of appeals that are either too data-heavy (boring) or too emotional (vague). It ensures your appeals answer the critical donor question: “What exactly will my gift accomplish?” by balancing concrete details with emotional resonance.
Sample prompt: “Help me write a fundraising appeal for our after-school program. Include that we serve 150 children daily, need $25,000 for supplies and snacks, and explain how this program keeps kids safe and learning while parents work.”
Stories that connect emotional appeal with concrete details help donors understand exactly how their support creates change.
4. Simplify Your Impact Reporting
Demonstrating accountability to donors, volunteers, and board members requires clear reporting. Copilot can transform complex data into accessible summaries that highlight your organisation’s effectiveness.
Why Copilot improves impact reporting: Copilot transforms complex program data into accessible language that resonates with different audiences – from board members who want specifics to community supporters who need the big picture story. It helps you present the same achievements in ways that are meaningful to each stakeholder group while maintaining accuracy and consistency.
Practical example: “Create a one-page summary of our annual impact: served 2,400 meals, trained 45 volunteers, operated on 89% program efficiency. Make it suitable for both major donors and community newsletter readers.”
Clear reporting builds trust and shows stakeholders that their support generates measurable results.
5. Maintain Consistent Community Engagement
Regular communication keeps your cause visible, and your community connected. Copilot helps maintain your social media presence with content that reflects your values and achievements.
Why Copilot improves community engagement: Copilot helps maintain your organisation’s authentic voice across all posts while ensuring you consistently highlight achievements and gratitude – elements that often get overlooked in busy periods. It enables you to maintain regular, meaningful communication even when your team is stretched thin, keeping supporters engaged and attracting new community members.
Practical example: “Write a Facebook post celebrating our partnership with the local school district to provide weekend meals for 75 students. Thank volunteers and explain how community support makes this program possible.”
Consistent messaging keeps supporters engaged and attracts new community members to your cause.
Making Technology Work for Your Mission
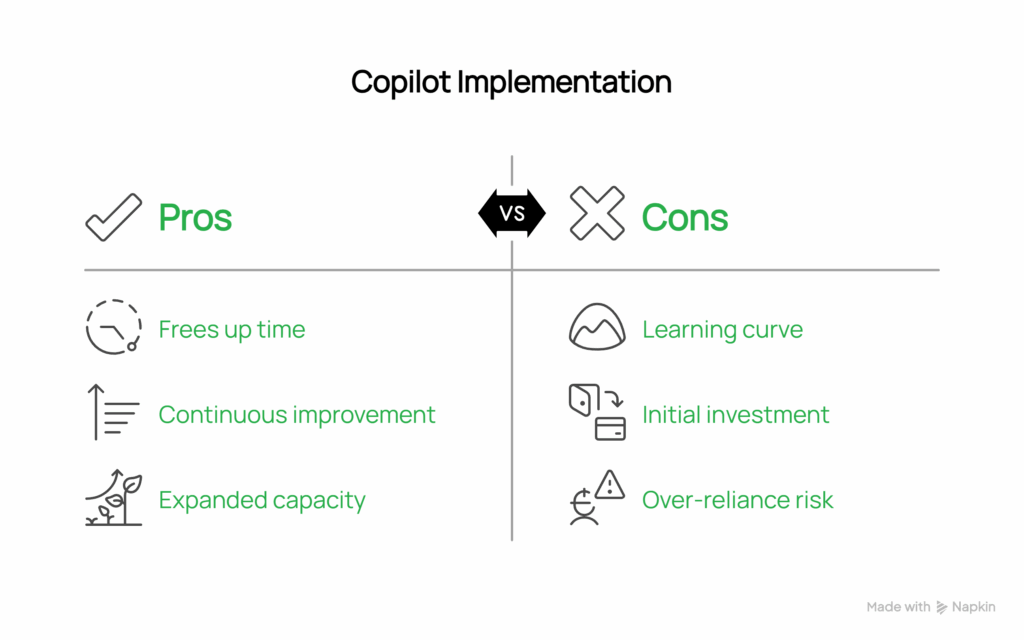
The key to success with Copilot isn’t replacing the human element that makes nonprofit work meaningful—it’s freeing up time so you can focus on what matters most: advancing your mission and serving your community.
Start small by choosing one area where you spend significant time on routine communications. Test Copilot’s capabilities, refine your approach based on results, and gradually expand to other areas. This measured approach ensures the technology truly serves your organisation’s needs.
Remember, effective use of AI tools like Copilot isn’t about perfection from day one. It’s about continuous improvement and finding ways to work smarter, not harder.
Ready to explore how Copilot can support your nonprofit’s growth? The investment in learning these tools today will pay dividends in expanded capacity to serve your community tomorrow.
At Grassroots IT, we help nonprofit organisations implement technology solutions that amplify their impact. Contact us to discuss how we can support your organisation’s technology strategy and growth.
Most Australian business owners spend their days jumping between different systems to understand what’s really happening in their company. You check Xero to see how the finances are tracking, hop into HubSpot to look at the sales pipeline, flick over to Shopify for e-commerce stats, then open Google Analytics to check website traffic. By the time you’ve pieced it all together, an hour’s gone—and you still don’t have the full story.
This fragmented approach to business intelligence isn’t just inefficient—it’s dangerous. When your critical business data lives in isolated silos, you’re making decisions with incomplete information. The solution isn’t to find better individual reports from each system, but to bring all that data together in one place where it can tell the complete story of your business.
Power BI integration with your existing business systems transforms scattered data points into strategic insights. But not all integrations deliver equal value. Here are the five essential data sources that Australian businesses should prioritise when building their business intelligence ecosystem.
1. Xero: The Financial Foundation
Xero dominates the Australian accounting software market for good reason—it handles everything from invoicing to payroll with remarkable efficiency. But where Xero truly shines in a Power BI environment is providing the financial context that transforms all your other business metrics from interesting to actionable.
When Power BI connects to your Xero data, you’re not just getting another way to view profit and loss statements. You’re creating the foundation for understanding whether your marketing spend is actually profitable, which customer segments drive the best margins, and how seasonal trends affect your cash flow. More importantly, you can see these insights in real-time rather than waiting for month-end reports.
The real power emerges when Xero financial data combines with information from your other business systems. Suddenly you can answer questions like “Which marketing campaigns deliver customers who actually pay their invoices on time?” or “How do our e-commerce profit margins compare to traditional sales channels?” These insights are impossible when your financial data stays trapped in accounting software.
2. SharePoint: Your Operational Backbone
Many Australian businesses already use Microsoft 365, making SharePoint a natural choice for storing operational data that doesn’t fit neatly into specialised software. Project timelines, inventory tracking, customer service records, and team performance metrics often live in SharePoint lists or shared Excel files.
The beauty of connecting SharePoint to Power BI lies in its flexibility. Unlike rigid database systems, SharePoint adapts to how your business actually works. Need to track project milestones? SharePoint handles it. Want to monitor equipment maintenance schedules? SharePoint works. Require a simple CRM for smaller clients who don’t warrant full HubSpot records? SharePoint delivers.
When this operational data flows into Power BI dashboards, it provides crucial context for understanding your business performance. You can correlate project delivery timelines with customer satisfaction scores or identify which operational bottlenecks impact financial results. This integration turns administrative data into strategic intelligence.
3. HubSpot: Sales Pipeline Visibility
For growing Australian businesses, HubSpot has become the CRM of choice because it scales from simple contact management to sophisticated marketing automation. The platform captures everything from initial lead sources to final deal closure, creating a comprehensive record of your sales and marketing activities.
Connecting HubSpot to Power BI transforms this sales data from historical reporting into predictive intelligence. Instead of just knowing how many leads you generated last month, you can forecast revenue based on current pipeline health, identify which lead sources convert to actual customers, and spot early warning signs when deals are likely to stall.
The integration becomes particularly powerful for Australian businesses operating across multiple channels or locations. You can compare performance between different sales teams, understand regional variations in customer behavior, and identify the marketing activities that actually drive qualified leads rather than just website visits.
4. Shopify: E-commerce Intelligence
Australian businesses increasingly operate hybrid models combining traditional sales with e-commerce platforms. Shopify has captured a significant portion of this market by making online selling accessible to businesses that previously relied solely on physical locations or direct sales.
Power BI integration with Shopify data reveals patterns that individual platform reports miss entirely. You can identify which products perform better online versus in-store, understand how seasonal trends differ between sales channels, and spot opportunities to optimise inventory across both physical and digital locations.
The real value emerges when Shopify data combines with your financial information from Xero. You can calculate true profitability by channel, understand the complete customer acquisition cost including shipping and processing fees, and make informed decisions about where to focus your growth efforts.
Google Analytics: Digital Marketing Context
Every Australian business with a website uses Google Analytics, but most barely scratch the surface of its insights. The platform captures detailed information about how potential customers discover your business, what they do on your website, and which content actually drives meaningful engagement.
When Google Analytics data flows into Power BI alongside your sales and financial information, it completes the customer journey picture. You can trace which marketing channels not only drive traffic but actually convert to paying customers. More importantly, you can calculate the true return on investment for your digital marketing efforts by connecting website behaviour to actual revenue.
This integration helps Australian businesses understand their digital presence beyond vanity metrics. Page views are interesting, but conversion rates that correlate with profitable customer acquisition are actionable intelligence.
The Power of Connected Business Intelligence
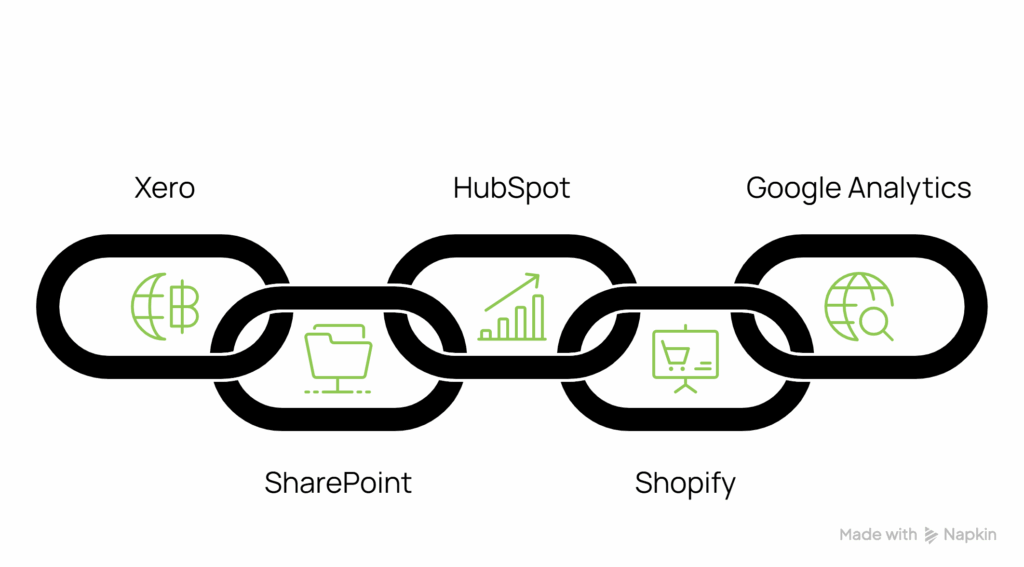
These five data sources work together to create a comprehensive view of your business operations. Financial performance from Xero provides the baseline. SharePoint adds operational context. HubSpot contributes sales intelligence. Shopify delivers e-commerce insights. Google Analytics completes the customer journey picture.
The technical complexity of connecting these systems, ensuring data accuracy, and building reliable dashboards can be high. But the business value of having all your critical information in one place—updating automatically and revealing patterns you’d never spot manually—justifies the investment.
When your business data works together instead of in isolation, you stop making decisions based on partial information and start operating with complete intelligence.
Ready to connect your business systems and gain complete visibility into your operations? We specialise in Power BI integration with Xero, HubSpot, Shopify, and other essential business platforms, helping Australian companies transform scattered data into strategic insights.
Picture this: your best field technician finishes a complex equipment inspection, spends thirty minutes filling out compliance paperwork in their truck, drives back to the office, and hands the forms to admin staff for data entry. Three days later, when the equipment actually fails, you discover the critical warning signs were buried in a stack of unprocessed paperwork on someone’s desk.
This scenario plays out across Australian businesses every day, from construction companies tracking safety inspections to service businesses managing customer visits. The information that could prevent problems, improve efficiency, or ensure compliance gets trapped in a paper-based bottleneck that transforms valuable field intelligence into administrative burden. Power Apps offers a proven solution to eliminate these inefficiencies.
The Real Cost of Paper-Based Field Data Collection
Most business owners understand that paper forms are inefficient, but the true cost goes far beyond obvious time wastage. When field data collection relies on clipboards and carbon copies, you’re creating multiple points of failure that compound into serious business risks.- Critical information delays: Safety hazards, equipment failures, and customer issues sit unaddressed while paperwork awaits processing
- Double data entry errors: Transcription mistakes corrupt carefully collected field observations during office data entry
- Lost documentation: Weather damage, misplaced forms, and illegible handwriting eliminate important business intelligence
- Compliance gaps: Missing signatures, incomplete inspections, and poor audit trails create regulatory risks
- Resource misallocation: Skilled field staff spend valuable time on administrative tasks instead of core activities
The Power Apps Transformation
Power Apps transforms field data collection by eliminating the gap between observation and action. Custom mobile solutions replace paper-based processes, enabling field staff to enter information directly into digital forms that immediately become available to the people who need to act on it.
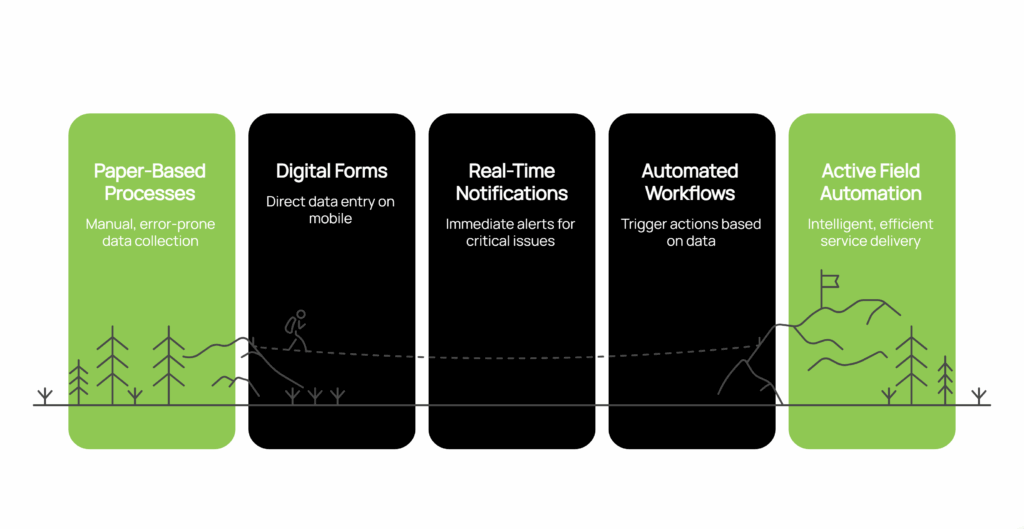
The transformation delivers measurable business improvements:
- Real-time problem resolution: Safety hazards trigger immediate supervisor notifications and corrective action workflows
- Automated compliance management: Digital forms enforce mandatory field completion while creating permanent audit trails
- Integrated business processes: Job completion automatically generates invoices, work orders, and customer communications
- Enhanced data accuracy: Eliminate transcription errors through direct digital capture with photos, GPS, and timestamps
- Offline reliability: Forms work without internet connectivity and sync automatically when signals return
- Professional customer experience: Clean, branded digital processes replace handwritten forms and carbon copies
The real power emerges through intelligent workflows that transform data collection from passive documentation into active field service automation. When a field inspection identifies a safety hazard, the system immediately notifies supervisors, generates work orders for remediation, and flags related equipment for monitoring.
Power Apps Applications Across Australian Industries
Construction companies use Power Apps for safety inspections that automatically generate compliance reports while creating photographic evidence of site conditions. When inspectors identify potential hazards, the system immediately alerts project managers and creates corrective action tasks with deadlines and responsibility assignments.
Equipment maintenance teams leverage mobile data collection for asset condition tracking that triggers predictive maintenance workflows. Field technicians scanning equipment barcodes can instantly access maintenance histories, update condition assessments, and automatically generate parts orders when wear indicators reach threshold levels.
Service businesses capture customer interaction data that flows directly into billing systems. Job completion forms with customer signatures automatically generate invoices, trigger follow-up communications, and update service histories without requiring office staff to process paperwork.
The Strategic Business Impact
Power Apps field data collection creates competitive advantages that extend far beyond operational efficiency improvements. Real-time visibility into field operations enables better resource allocation, faster problem resolution, and more accurate job costing. Management dashboards displaying current field activities help business owners make informed decisions about priorities and resource deployment.
Compliance management becomes systematic rather than reactive when Power Apps digital forms enforce mandatory completion and automatically generate audit trails. Customer satisfaction improves when field data flows immediately into customer service systems, enabling faster response times and more professional digital processes.
Making the Transformation
The technical complexity of building effective mobile data collection systems, ensuring reliable offline functionality, and integrating with existing business systems requires working with an experienced Power Apps consultant. However, the business benefits of eliminating paper-based field processes typically deliver return on investment within months rather than years.
When field staff can focus on their core expertise instead of administrative tasks, and when critical information becomes available in real-time rather than after processing delays, the entire business operates more efficiently and effectively.
Ready to transform how your field teams collect and share critical business information? Our mobile app development services specialise in Power Apps solutions that eliminate paper-based processes, enabling real-time field data collection that integrates seamlessly with your existing business systems. Contact us to explore how Power Apps can revolutionise your field operations.
The Reality Check Every SMB Leader Faces
You open your cyber insurance renewal and see a 40% premium increase. Again. The fine print highlights “required security controls” and references frameworks you’ve never heard of. Meanwhile, one of your key clients just sent a vendor security questionnaire asking about your “cybersecurity maturity framework.”
This isn’t just paperwork, it’s the new cost of doing business. Australian SMBs are discovering that basic antivirus and backups no longer satisfy insurers, clients, or compliance requirements. The challenge isn’t just implementing better security; it’s finding a structured approach that delivers enterprise-level protection without enterprise-level complexity. Referencing a cybersecurity compliance checklist can streamline this process. This highlights the growing importance of cybersecurity for SMBs.
Modern cybersecurity requires layered defences, documented processes, continuous monitoring, and measurable outcomes. Yet most security frameworks were designed for large enterprises with dedicated security teams and unlimited budgets.
That’s exactly why SMB1001 exists—the cybersecurity framework purpose-built for businesses with 5-200 employees.
The Business Case for Structured Security
Before diving into technical details, let’s address the financial reality. Cybersecurity incidents don’t just cost money. They disrupt operations, damage client relationships, and can permanently impact your reputation. Meanwhile, cyber insurance premiums continue rising while coverage becomes more restrictive.
What we’re seeing across our client base is clear: businesses with documented security frameworks experience faster vendor approval processes, reduced insurance scrutiny, and access to opportunities that were previously out of reach.
The revenue opportunity is significant. Enterprise clients increasingly require vendor security assessments before engagement, and demonstrable alignment with the SMB1001 standard satisfies most security questionnaires. This opens doors to contracts and partnerships that security-conscious organisations simply won’t consider without proper documentation. This highlights the growing importance of cybersecurity for SMBs.
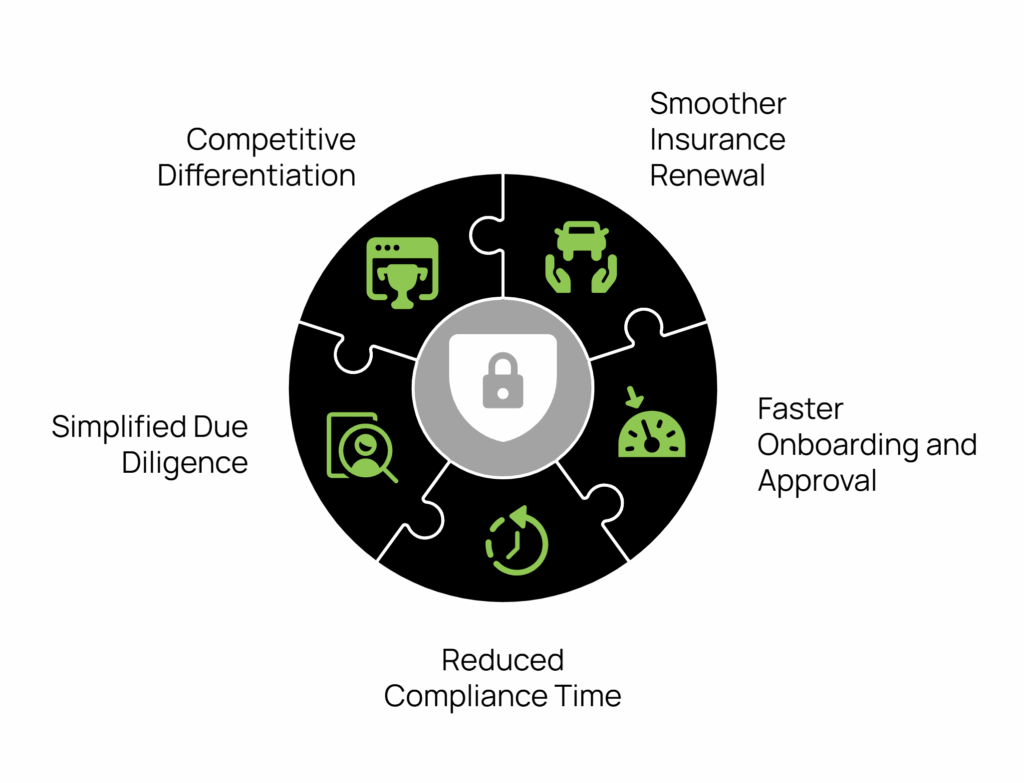
Structured security implementation delivers measurable business benefits:
- Smoother insurance renewal processes with better terms
- Faster vendor onboarding and client approval cycles
- Reduced time spent on security questionnaires and compliance preparation
- Simplified due diligence for partnerships and potential acquisitions
- Clear competitive differentiation in security-conscious markets
What Makes SMB1001 Different
Established cybersecurity frameworks like ISO 27001 and NIST are excellent, comprehensive standards that have proven their value across thousands of organisations worldwide. The challenge? These frameworks were designed for enterprises with dedicated security teams, substantial budgets, and complex organisational structures.
“SMB1001 takes the proven security principles from these established frameworks and adapts them specifically for smaller organisations—making enterprise-level cybersecurity both practical and achievable for growing businesses.”
The SMB1001 framework delivers this practical approach through four key characteristics that address the specific challenges growing businesses face:
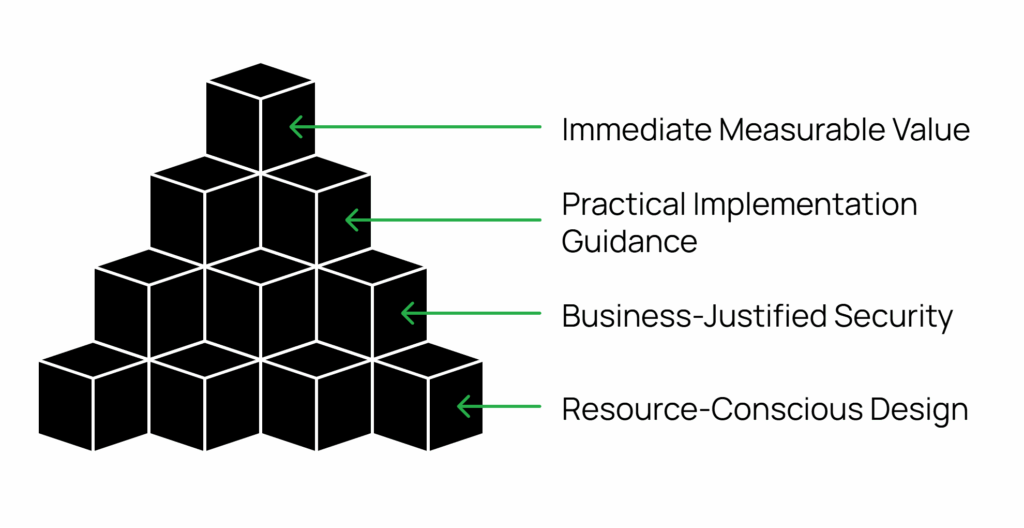
Resource-Conscious Design: Every control is evaluated against implementation cost and ongoing maintenance requirements. No recommendations require dedicated security staff or enterprise-grade budgets.
Business-Justified Security: Rather than generic best practices, each security measure directly ties to protecting your revenue, reputation, and operational continuity. This approach ensures businesses understand not just what to implement, but why it matters to their specific business model.
Practical Implementation Guidance: Step-by-step processes your existing team can follow without specialised cybersecurity expertise, supported by templates, checklists, and decision trees that eliminate guesswork.
Immediate Measurable Value: Quick wins and visible improvements establish momentum while building toward comprehensive protection that scales with your growth.
The Three-Tier Approach That Scales with Your Business
Bronze Level: Essential Security Foundation
Perfect for establishing baseline protection and meeting basic compliance requirements. Achieving Bronze-level alignment addresses the most common attack vectors and can typically be accomplished within 6-8 weeks. Referencing a cybersecurity compliance checklist can streamline this process.
Core implementations:
- Complete asset inventory and management systems
- Strong authentication policies with multi-factor authentication
- Documented incident response procedures
- Regular security awareness training program
- Reliable backup and recovery systems
Business outcome: Satisfies most insurance and basic client security requirements while dramatically reducing your exposure to common attack vectors.
Silver Level: Advanced Protection and Monitoring
Designed for businesses handling sensitive data or operating in regulated industries. Silver builds advanced capabilities on your Bronze foundation over an additional 8-10 weeks.
Enhanced capabilities:
- Advanced threat detection with automated response
- Network segmentation protecting critical systems
- Regular vulnerability assessments with remediation tracking
- Comprehensive backup strategy with tested recovery procedures
- Third-party vendor security assessments
Business outcome: Documented security controls needed for enterprise client contracts while significantly reducing successful cyberattack risk.
Gold Level: Cyber Resilience as Strategic Asset
Full cyber resilience for organisations viewing cybersecurity as a competitive advantage. Gold-level organisations often see security transform from cost centre to revenue driver.
Advanced capabilities:
- Continuous security monitoring with 24/7 threat response
- Business continuity planning with regular testing
- Supply chain security management
- Organisation-wide security culture integration
- Regular independent security assessments
Business outcome: Win contracts specifically because of your security posture. Access previously restricted markets where security certification is mandatory.
Your Implementation Path Forward
Rather than overwhelming you with detailed project plans, SMB1001 focuses on sustainable progress through clear phases:
Foundation Phase: Comprehensive security assessment establishes your baseline and identifies quick wins. Basic access controls and password policies provide immediate risk reduction.
Core Controls Phase: Deploy essential systems including asset management, incident response procedures, and reliable backups. Complete initial staff security training and document key policies.
Assessment Phase: Evaluate your implementation against Bronze-level requirements and address any remaining gaps. Establish a baseline for potential advancement to silver or gold levels.
Why Acting Now Creates Competitive Advantage
The cybersecurity landscape continues evolving rapidly. Regulatory requirements expand, insurance standards rise, and client expectations grow more sophisticated. The organisations implementing structured cybersecurity frameworks today position themselves as trusted partners for tomorrow’s opportunities. These are part of the evolving cyber insurance requirements.
More critically, cyber threats evolve daily. Every day without proper security controls exponentially increases your exposure to incidents that could devastate operations and reputation.
SMB1001 cybersecurity framework isn’t about achieving perfect security overnight, it’s about building practical, sustainable cybersecurity that fits your business reality. Whether you need Bronze-level alignment to satisfy current requirements or Gold-level maturity to pursue enterprise opportunities, the framework provides a clear, achievable path forward.
Take Your First Step Toward Strategic Security
The question isn’t whether you’ll eventually need structured cybersecurity, it’s whether you’ll implement it proactively or be forced into it reactively after an incident.
Our SMB1001 Gap Assessment Audit identifies your current security posture and maps your most efficient path to certification. Get clarity on your cybersecurity journey with a practical evaluation of your existing controls and priority improvements.
Transform cybersecurity from a compliance burden into a strategic business asset. Your future self will thank you.
Excel has been the backbone of business reporting for decades, and honestly, it’s brilliant at what it does. Most growing businesses start their reporting journey there, and for good reason—it’s familiar, flexible, and everyone knows how to use it.
But here’s the thing: Excel reporting can quietly become your biggest productivity drain without you even realising it. After helping businesses with their technology for almost 20 years, We’ve seen this pattern play out countless times. What starts as a simple monthly report gradually evolves into a complex web of spreadsheets that consumes hours of valuable time each month.
When Excel Still Makes Perfect Sense
Don’t get me wrong—Excel isn’t the enemy here. We still see plenty of situations where it’s absolutely the right tool for the job. Take those quarterly board reports or annual summaries, for instance. If you’re pulling together information that doesn’t change frequently and you’re comfortable with the manual process, Excel handles this beautifully.
Similarly, if you’re working with smaller datasets—maybe hundreds or a few thousand rows—Excel manages this without breaking a sweat. And when you need to quickly analyse a specific problem or dive into a one-off investigation, Excel’s flexibility makes it perfect for that kind of exploratory work.
The sweet spot for Excel remains those static reports that don’t change much and where you’re genuinely happy updating them manually each period. There’s nothing wrong with this approach if it’s working for your business.
The Moment Everything Changes
But there’s usually a moment when businesses realise their Excel reporting has quietly taken on a life of its own. We call it “spreadsheet archaeology”— hunting through different versions to find the “final final FINAL” report.
Or maybe you’ve noticed that preparing your monthly reports now takes an entire day instead of the hour it used to take. You’re copying and pasting data from your CRM, then your accounting system, then that other database, and by the time you’re finished, you’re already thinking about how you’ll need to do it all again next month.
The real wake-up call often comes when a key person goes on holiday and suddenly no one else knows how to update the reports. I’ve seen businesses scramble for weeks.
More troubling is when data accuracy becomes a guessing game. Different report versions tell different stories because they were created at different times using different sources. Management meetings become exercises in figuring out which numbers are correct.
Another common frustration is when your reports start hitting Excel’s performance limits. Files that take forever to open, constant crashes when you try to refresh data, or worse—losing work because the file corrupted. These aren’t just minor inconveniences; they’re signals that you’ve outgrown what spreadsheet-based reporting can reliably deliver.
Business Intelligence Benefits: Power BI for Australian Companies
Power BI isn’t about creating prettier reports, though they certainly look more professional. It’s about solving these very real business problems that Excel reporting creates as you grow.
The biggest transformation comes from connecting your reports directly to your data sources. Instead of manually gathering information from your CRM, accounting system, and various databases each month, Power BI pulls this data automatically. That monthly day of preparation becomes a few minutes of reviewing updated dashboards that refresh themselves.
This automation means you’re always working with current data rather than month-old snapshots. When a potential customer asks about your latest performance metrics, or when you need to make a quick decision based on recent trends, the information is already there, reflecting what’s actually happening in your business right now.
The consistency factor can’t be overstated either. When everyone in the business is working from the same data source, those frustrating “which version is correct?” conversations disappear. Your sales manager, operations team, and financial controller are all looking at the same numbers, updated at the same time, eliminating confusion and building confidence in your business intelligence.
Power BI also handles much larger datasets without Excel’s performance issues. Reports stay fast and responsive as your data grows, with no corruption risks.
Key Signs It’s Time to Make the Switch

The clearest indicator that Excel reporting has become counterproductive is when data preparation consumes more time than data analysis. Australian businesses typically reach this tipping point when they’re spending several hours each month just gathering and formatting data before meaningful analysis can begin. Other warning signs include team members working with different versions of the same report, creating compliance risks around data accuracy, and critical business intelligence depending on one person’s Excel expertise.
Excel to Power BI Migration: Professional Implementation
The beauty of working with experienced professionals is that you don’t need to worry about learning new software or managing the technical complexity. We handle the entire transition process, from connecting your data sources to building the dashboards that will replace your current Excel reports.
The process typically starts with understanding your current reporting needs and pain points. We’ll look at your existing Excel reports, identify which data sources they draw from, and design Power BI solutions that not only replicate what you have but enhance it with real-time updates and better visualisation.
Most businesses are surprised at how quickly they see results. Within a few weeks, what used to be a day-long monthly reporting exercise becomes a quick review of automatically updated dashboards. The time savings alone usually justify the investment, but the improved accuracy and timeliness of information often proves even more valuable for decision-making.
The Bottom Line
Your time is valuable, and business intelligence solutions should accelerate decision-making, not hinder it. If monthly reporting is a burden rather than providing valuable insights, automated dashboards and data visualisation tools offer a proven path forward.
The transformation from manual Excel processes to automated Power BI reporting typically delivers measurable ROI within 90 days for Australian businesses. When spreadsheet archaeology becomes a monthly ritual, that’s technology working against your business growth rather than enabling it.
Ready to explore automated reporting solutions for your business? We help Australian businesses transition from Excel to Power BI dashboards, handling the technical complexity while you focus on using better business intelligence for growth.
Why Information Management Is the Strategy Behind Every Smart Business Move
When business leaders evaluate their operational costs, they naturally focus on the obvious expenses: payroll, rent, equipment, software licenses. These line items are clearly defined, easily tracked, and regularly scrutinised.
But there’s another cost category that rarely appears on any budget report yet quietly drains resources from every growing business: scattered information systems. This hidden expense compounds daily, impacting everything from decision-making speed to competitive positioning, often without leadership fully recognising its scope.
While you’re focused on driving growth, increasing efficiency, and protecting your business, your team is quietly losing productivity to information chaos—and it’s costing more than you realise.
The True Cost of Information Scattered Across Systems
The real expense isn’t in the technology—it’s in the compound effect of small inefficiencies.
For example:
- When your office manager spends an hour searching through email attachments for the latest employee handbook because three different versions exist.
- When your growing business loses a client opportunity because the proposal approval got stuck in someone’s inbox while they were traveling.
- When your nonprofit’s grant application gets delayed because the required compliance documentation is scattered across multiple team members’ computers.
These aren’t dramatic failures—they’re quiet productivity drains that accumulate into significant competitive disadvantages. While your team manages information chaos, your competitors with streamlined systems are focusing that same energy on winning new clients, securing funding, and scaling operations.
The Strategic Framework for Information Management
Smart business leaders approach information management the same way they approach any other critical business function: strategically. A well-designed information architecture directly influences:
Effective Collaboration Techniques:
- Decision-making speed: How quickly can leadership access the insights they need?
- Operational efficiency: How seamlessly do your teams collaborate on projects?
- Compliance readiness: How confidently can you demonstrate audit trails and document control?
- Scalability: How well will your systems support growth without breaking?
Beyond Band-Aid Solutions: Addressing the Root Cause
Many growing businesses attempt to solve information chaos by adding more tools—another cloud storage service here, a project management app there. However, this approach often amplifies the problem by creating more disconnected systems.
The fundamental issue isn’t storage capacity or individual tool functionality. It’s the lack of a unified information ecosystem that grows with your business while maintaining security and simplicity.
Smart organisations recognise that effective information management requires three core capabilities:
- Findability: Any team member can locate any document within seconds, regardless of who created it or when
- Collaboration: Teams can work together on documents in real-time while maintaining clear version control and approval processes
- Security: Information access is controlled, auditable, and compliant with your industry requirements
The Microsoft 365 Integration Advantage: Why Unified Systems Drive Growth
Forward-thinking organisations recognise that their technology stack should amplify human capability, not complicate it. This is where strategic integration becomes crucial—and why Microsoft 365 with SharePoint provides a strong foundation for scalable businesses.
When your information management seamlessly connects with the communication and productivity tools your team already uses, several transformative things happen:
- Adoption becomes natural: Teams don’t need to learn entirely new systems or change established workflows
- Efficiency multiplies: The same action (saving a document, updating a project status) triggers updates across multiple business processes
- Visibility increases: Leadership gains real-time insights into project progress, resource allocation, and team productivity
- Compliance simplifies: Rather than managing permissions and audit trails across multiple systems, everything operates under consistent, enterprise-grade security protocols
Turning Information Management into Competitive Advantage
The most successful SharePoint implementations we’ve seen don’t just solve existing problems—they unlock new capabilities that weren’t previously possible:
- Automated workflows: Eliminate manual approval bottlenecks, allowing your team to focus on strategic work rather than process management
- Real-time insights: Provide leadership with immediate visibility into project status, resource allocation, and operational efficiency
- Scalable processes: Ensure that information systems enhance rather than constrain growth, supporting new team members, locations, and business complexity without requiring complete overhauls
- Compliance simplifies: Rather than managing permissions and audit trails across multiple systems, everything operates under consistent, enterprise-grade security protocols
The competitive advantage becomes clear when your organisation can respond to client requests immediately because all relevant information is instantly accessible. Strategic decisions improve when they’re based on complete, current data rather than incomplete snapshots. New team members become productive from day one because information is organised and findable. Most valuable for growing businesses: compliance readiness becomes instant rather than a scrambling exercise when auditors arrive.
The Implementation Mindset: Strategic, Not Tactical
Successful information management transformation requires approaching the challenge strategically rather than tactically. This means starting with clear business outcomes—defining what success looks like in terms of reduced decision-making time, improved project delivery, or enhanced compliance readiness. Smart organisations design for growth from the beginning, ensuring their solution can adapt as teams double in size, expand to multiple locations, or develop more complex approval workflows.
Equally important is planning for adoption by leveraging existing tools and workflows rather than forcing dramatic changes that create resistance. Finally, security must be prioritised from day one, implementing enterprise-grade protections that maintain compliance requirements while actually improving accessibility for authorised users.
Your Next Strategic Decision
Every day your organisation operates with scattered information systems, you’re making an unconscious choice to accept inefficiency, security risks, and missed opportunities.
The question isn’t whether to address this challenge—it’s whether to approach it strategically or continue managing it reactively.
Smart business leaders recognise that information management isn’t an IT project—it’s a business transformation that directly impacts growth, efficiency, and competitive positioning.
The organisations that thrive in the coming years will be those that turn information chaos into strategic advantage. The technology exists. The question is whether you’ll use it strategically.
Ready to transform information chaos into competitive advantage with SharePoint?
At Grassroots IT, we help growing businesses implement strategic Microsoft SharePoint solutions that scale with their ambitions. Our approach focuses on understanding your unique challenges and designing unified information management systems that enhance rather than complicate your operations.
Contact us today to discuss how strategic information management can accelerate your business objectives.
For most businesses today, technology plays a central role in daily operations. From communication and collaboration to data storage and customer service, reliable IT systems are essential. However, without a dedicated IT team, handling these systems internally it can quickly become overwhelming.
When staff are pulled away from their roles to deal with IT issues, productivity suffers. Unplanned downtime, slow systems, and security risks all create barriers that stop your team from working efficiently. Over time, these disruptions can affect not just performance but overall business growth.
This is where a managed IT service becomes valuable. Rather than waiting for things to break, managed services focus on preventing issues before they happen. They ensure your systems are maintained, monitored, and supported consistently, helping you reduce risk, avoid downtime, and give your team the tools and confidence to do their jobs effectively.
What Is a Managed IT Service – and Why It’s More Than Just Tech Support
A managed IT service is an ongoing partnership where a third-party provider takes responsibility for monitoring, maintaining, and supporting a business’s technology. Instead of relying on ad hoc repairs or internal staff to fix problems as they arise, businesses gain consistent support that keeps systems running efficiently.
This approach reduces downtime, strengthens security, and helps teams work without interruptions. It includes everything from helpdesk support and system updates to strategic planning and cloud services. By covering both day-to-day issues and long-term IT needs, a managed service takes the pressure off internal teams.
More importantly, it’s not just about fixing problems, it’s about preventing them. A managed IT service helps businesses stay ahead of potential issues, improve system performance, and align their technology with their broader goals.
When IT runs smoothly, people work better. That’s the real value behind managed services.
What You Actually Get With a Managed IT Service
A managed IT service includes more than just reactive support. It covers a full range of services designed to keep your systems secure, reliable, and aligned with how your business operates.
Proactive Monitoring and Maintenance
Your systems are monitored around the clock to catch issues early. Regular maintenance helps prevent outages, slowdowns, and performance drops before they impact your team.
Unlimited Helpdesk Support
When problems do arise, fast and friendly help is only a call or ticket away. Whether it’s a forgotten password or software not loading, your staff can get back to work quickly with expert support.
Cybersecurity Management
Security risks are constantly evolving. A managed service includes cybersecurity protection like firewalls, antivirus, multi-factor authentication, and backup systems to help keep your data safe and your operations secure.
Cloud Services and Microsoft 365
Modern businesses rely on cloud platforms to stay flexible and productive. Managed services include setup and ongoing support for tools like Microsoft 365, cloud storage, and remote access solutions.
Strategic IT Planning
Technology should support your growth, not slow it down. Managed services include regular reviews and planning sessions to make sure your IT systems match your business goals and can scale with your needs.
IT Project Support
When it’s time to upgrade systems, onboard new tools, or improve your setup, a managed IT provider can plan and deliver projects with minimal disruption to your business.
Signs You’re Ready for a Managed IT Service
Not every business starts with managed IT support, but there’s a point where managing tech internally starts to cost more than it saves. If you’re seeing any of the signs below, it may be time to make the switch.
Frequent IT Problems
If you’re dealing with the same issues over and over – like slow systems, dropped connections, or security warnings, it’s a sign your current setup isn’t keeping up.
Staff Handling IT on the Side
When employees are pulled away from their actual jobs to troubleshoot IT problems, productivity drops. It also increases the risk of errors or missed updates.
No Long-Term IT Plan
If your technology setup has grown without structure, it may be holding your business back. Managed IT services can help you build a plan that supports future growth.
Security Concerns
Outdated systems and weak protections leave your business open to threats. Managed IT services ensure you have up-to-date security measures in place.
Growing or Changing Business Needs
Whether you’re hiring more staff, opening new locations, or moving systems to the cloud, a managed IT service can support you through the change without added stress.
Why Businesses Choose Grassroots IT for Managed Services
At Grassroots IT, we don’t take a one-size-fits-all approach. We take the time to understand how your business works so we can provide support that fits your team, your systems, and your goals.
Our Brisbane-based team becomes an extension of your business, offering reliable support with a personal touch. From day one, we focus on building a strong relationship, not just delivering a service. That means clear communication, fast response times, and a consistent commitment to helping your team succeed.
We partner with trusted platforms like Microsoft and HP to ensure the solutions we provide are reliable, secure, and built to support your growth.
When your technology works, your people work better. That’s what we’re here to support – every day.
Let’s Help Your Team Thrive
Managing technology shouldn’t be a distraction. With the right support, your systems can run smoothly, your team can stay productive, and your business can grow without unnecessary delays or risks.
Grassroots IT is here to help make that happen. We work as a true partner, offering managed IT services that support your goals, remove roadblocks, and keep your business moving forward.
Want to see how it could work for your team? Get in touch with us today.