ISO 27001 Certified
Framework - Aligned
Brisbane - Based
Practical Recommendations
The Challenge
Most business leaders we speak with have a nagging sense that their cybersecurity could be better—but they’re not sure exactly where the gaps are, how serious they might be, or what to prioritise fixing first.
You’ve probably got MFA enabled, your backups are running, and you’ve invested in some security tools. But are they configured properly? Are there blind spots you’re not aware of? If something happened tomorrow, would you actually be protected?
The uncertainty itself is the problem. Without a clear picture of your current security posture, you can’t make informed decisions about where to invest your time and budget. You might be over-investing in areas that are already adequate while leaving critical gaps unaddressed.
A cybersecurity audit cuts through that uncertainty. It gives you an honest, independent assessment of where you stand—and a practical roadmap for where to go next.
Why An Audit?
You're Not Sure Where You Stand
If you can’t confidently answer the question “how secure are we?”—or if the answer is “I think we’re okay”—an audit provides the clarity you need. You’ll know exactly what’s in place, what’s missing, and what’s configured incorrectly.
Your Insurer or Clients Are Asking Questions
Cyber insurance applications and client security questionnaires require you to make specific claims about your security controls. An audit ensures you can answer honestly and confidently—and identifies gaps you need to close before making those claims.
You're Planning a Security Investment
Before spending money on new security tools or services, it makes sense to understand what you actually need. An audit identifies your highest-priority gaps so you can invest where it matters most rather than buying solutions to problems you don’t have.
Your Business Has Changed
Growth, new staff, remote work, cloud migration, new systems—any significant change can introduce security gaps. If your business looks different than it did two years ago, your security posture may have drifted without anyone noticing.
You Want an Independent View
If your current IT provider tells you everything is fine, how do you verify that? An independent audit from a different set of eyes provides assurance—or identifies issues that might have been missed.
What We Assess
What Our Cybersecurity Audit Covers
Our audit is comprehensive but practical—we assess what actually matters for businesses your size, not theoretical enterprise concerns. We evaluate your security posture across several key domains:
Identity and Access Management:
How users authenticate, password policies, MFA implementation, privileged access controls, account lifecycle management, and access to sensitive systems.
Endpoint Security:
Device protection, antivirus/EDR configuration, patch management, encryption status, and mobile device controls.
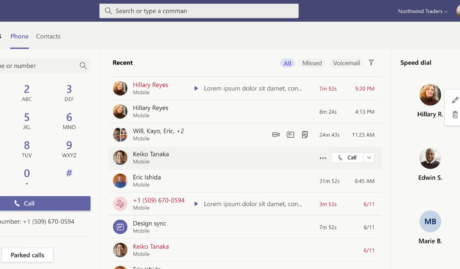
Email and Collaboration Security:
Phishing protection, email authentication (SPF/DKIM/DMARC), external sharing controls, and Microsoft 365 security configuration.
Data Protection
Backup configuration and testing, data classification, retention policies, and protection of sensitive information.
Network Security:
Firewall configuration, network segmentation, remote access controls, and wireless security.
Security Governance:
olicies and procedures, incident response readiness, security awareness, and vendor management.
Framework Alignment:
Where relevant, we assess your position against recognised frameworks like Essential 8 or SMB1001, giving you a baseline for certification or compliance work.
Why Grassroots IT
Why Brisbane Businesses Choose Us
We've Done It Ourselves
Grassroots IT is ISO 27001 certified. We’ve been through rigorous security audits ourselves—we understand both sides of the process. When we assess your security, we bring the perspective of an organisation that has implemented and maintained the controls
we’re evaluating.
Practical Recommendations, Not Theoretical Perfection
We understand SME realities—limited budgets, small teams, competing priorities. Our recommendations are prioritised by risk and achievability. We tell you what matters most and what can wait, not just what’s theoretically ideal.
Microsoft Specialists
Most of our clients run Microsoft 365, and we know the platform deeply. We assess not just whether you have the right security tools, but whether they’re configured correctly—often uncovering significant gaps in environments that look fine on the surface.
No Obligation to Engage Further
Our audit is genuinely independent. You’ll receive a comprehensive report and recommendations regardless of whether you engage us for remediation. Many businesses take our findings to their existing IT provider—and that’s perfectly fine. The audit stands on its own merit.
Local Team, Real Conversations
We’re based in Brisbane and we present our findings in person (or via video if you prefer). You’ll have a real conversation about what we found—not just a document dropped in your inbox. We explain the ‘so what’ behind every finding.
How It Works
Our Audit Process
Scoping Conversation
We start with a conversation to understand your business, your concerns, and what’s driving the audit. This helps us focus on what matters most to you and ensures there are no surprises about scope or cost.
Information Gathering
We collect information about your environment—existing documentation, system configurations, and policies. For technical assessment, we use read-only access to review your Microsoft 365 tenant, network configurations, and security tools.
Technical Assessment
Our team evaluates your security controls against recognised frameworks and industry best practices. We assess what’s in place, how it’s configured, and where the gaps are. This includes both automated scanning and manual expert review.
Analysis and Prioritisation
We analyse our findings and prioritise them by risk level and remediation effort. Not everything we find will be critical—we help you understand what needs immediate attention versus what can be addressed over time.
Report and Presentation
You receive a comprehensive written report with our findings and recommendations. We present this in person, walking you through what we found and answering your questions. The report is written in plain language—not security jargon.
Roadmap Discussion
We discuss practical next steps—what to tackle first, realistic timelines, and options for implementation. Whether you want our help with remediation or prefer to work with your existing provider, you’ll leave with a clear path forward.
What You Get
Executive Summary:
A high-level overview suitable for sharing with leadership or your board—key findings, overall risk assessment, and priority recommendations.
Detailed Findings Report:
Comprehensive documentation of each finding with risk rating, current state, recommended state, and remediation guidance.
Prioritised Remediation Roadmap:
A practical action plan organised by priority, with estimated effort levels to help you plan resources and budget.
Framework Alignment Score:
Where relevant, your current position against Essential 8, SMB1001, or other frameworks—useful for certification planning or compliance evidence.
Presentation Session:
A face-to-face (or video) session to walk through findings, answer questions, and discuss next steps.
Ready to Know Where You Stand?
Whether you’re responding to an insurer’s questions, preparing for a
compliance requirement, or simply want clarity on your security posture,
we can help. Book a conversation to discuss your situation and
understand what an audit would involve for your organisation.
Frequently Asked Questions
How long does a cybersecurity audit take?
For most SMEs (20-100 staff), the assessment takes 2-3 weeks from start to final presentation. The actual time we need from your team is minimal—typically a few hours for initial information gathering and access setup, plus the final presentation session.
How much does an audit cost?
Audit pricing depends on the size and complexity of your environment. We provide a fixed quote after our scoping conversation so you know exactly what to expect—no surprises. Contact us to discuss your specific situation and receive a tailored quote.
Will you find problems? What if everything is fine?
We’ve never completed an audit without finding areas for improvement—that’s not a criticism, it’s the nature of cybersecurity. Even well-managed environments have gaps. If your security posture is genuinely strong, we’ll confirm that and identify the minor improvements that could make it even better.
Do we have to use you for remediation?
No. The audit is a standalone service. You receive a complete report and recommendations regardless of whether you engage us for any follow-up work. Many clients take our findings to their existing IT provider, and that works well. Others prefer us to help implement the recommendations—we’re flexible either way.
What access do you need to our systems?
We use read-only access wherever possible. For Microsoft 365 assessment, we need Global Reader access to review configurations. For network assessment, we may need read access to firewall rules and documentation. We never make changes to your environment during an audit.
How often should we have an audit?
We recommend a comprehensive audit every 1-2 years, or whenever your business undergoes significant change (growth, new systems, cloud migration, office relocation). Between audits, ongoing security monitoring and regular reviews help maintain your posture.
Can the audit help with our cyber insurance application?
Yes. Our audit identifies the controls insurers typically ask about and confirms whether you have them in place. The report can serve as evidence for insurance applications, and our recommendations help you close gaps before making claims on your application.
What's the difference between an audit and a penetration test?
A penetration test attempts to actively exploit vulnerabilities to see if an attacker could breach your systems. An audit is broader—it assesses your overall security posture, policies, configurations, and controls. Most SMEs benefit more from an audit than a penetration test; the audit identifies foundational gaps that should be addressed before investing in penetration testing.