Why Knowing Cybersecurity Is Important Isn't Enough
Every business leader knows cybersecurity matters. Yet most still struggle to make meaningful progress. The problem isn’t awareness – it’s knowing what to do next.
Most Brisbane business leaders we speak to can articulate the cybersecurity risks their business faces. They’ve read the breach headlines. They know their clients are asking harder questions. They understand the insurance market has changed.
Awareness is no longer the problem.
What most businesses haven’t solved is what comes after awareness: making confident, informed decisions about what to actually do. Ask a business leader what specifically they’re working on, how they decided those were the right priorities, and how they measure progress and that’s usually where the certainty evaporates.
The Awareness Plateau
Over the past decade, cybersecurity awareness has skyrocketed. Businesses understand the risks. They’ve read the headlines about ransomware attacks. They know client data needs protecting. They’re aware insurance companies are asking harder questions.
Awareness is no longer the problem.
The problem is what comes after awareness: making informed decisions about what to actually do.
Most businesses get stuck on what we call the Awareness Plateau. They know cybersecurity matters, but without expertise to guide decisions, they’re left guessing:
- Should we invest in a new firewall or focus on user training first?
- Is multi-factor authentication more urgent than application control?
- Should we commission another security audit or actually implement the last one?
- How do we know if we’re making real progress or just ticking boxes?
These aren’t questions about whether cybersecurity matters. They’re questions about how to make progress when you don’t have internal expertise to guide the journey.

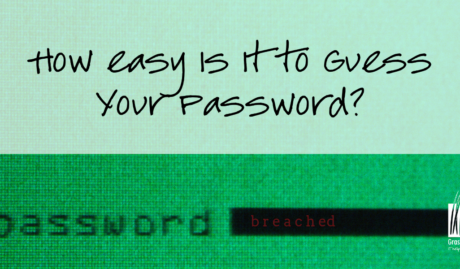
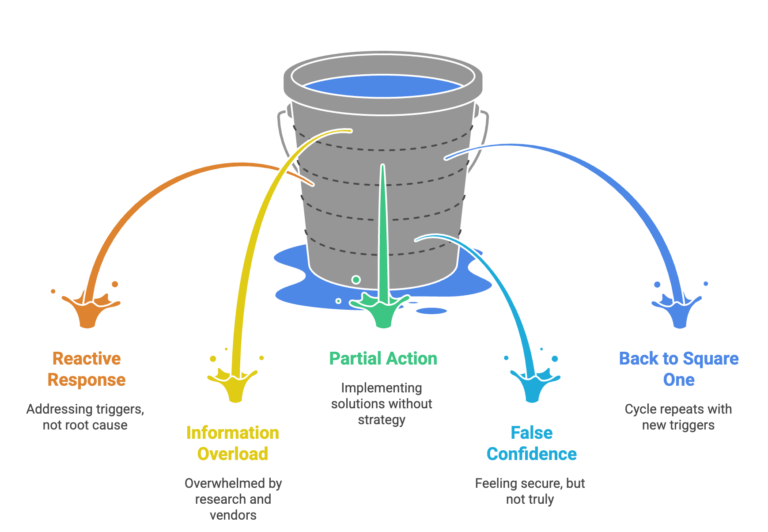
The Decision Dilemma
Here’s what the decision-making process looks like for most businesses without dedicated cybersecurity expertise, and it tends to follow a familiar pattern.
Something triggers concern: a client questionnaire, an insurance renewal, a news story about a breach that hits close to home. So the research begins. Google returns millions of results, every vendor claims their solution is the critical one, and the more you read, the more overwhelming it becomes.
Eventually, something gets implemented, usually whatever seemed most urgent or was recommended by the last person you spoke to. A firewall upgrade, a security audit, a new backup solution. For a while, it feels like progress. The immediate concern is addressed and security feels handled.
Then, six months later, another trigger arrives. A different client questionnaire. A new insurance requirement. And the realisation sets in: you’re still not confident about your overall security posture. You still don’t know if you’re focusing on the right things. You’re back to square one.
This cycle repeats because the underlying problem hasn’t changed: security decisions are being made without security expertise to guide them.
Why General IT Support Isn't Enough
Many businesses assume their IT support provider handles cybersecurity. And in a sense, they do – but there’s a critical distinction most people miss.
Your IT support keeps your environment secure operationally. They patch systems, configure firewalls, manage antivirus, respond to incidents, and maintain security configurations. This is essential – it’s your security foundation.
But operational security and strategic security are different capabilities:
Operational Security (What IT Support Provides):
- Keeping systems patched and updated
- Maintaining secure configurations
- Responding to security incidents
- Implementing technologies when requested
- Following best practices
Strategic Security (The Missing Layer):
- Assessing current maturity against recognised frameworks
- Prioritising improvements based on risk and business context
- Building systematic capability over time
- Collecting evidence for certifications and audits
- Demonstrating maturity to insurers, clients, and regulators
Think of it this way: operational security keeps your house locked and the alarm working. Strategic security ensures you’re protecting the right rooms, meeting building codes, and can prove it to your insurer.
You need both. But most businesses only have the operational layer.
The Framework Gap
When businesses do seek strategic guidance, they often turn to security frameworks like Essential Eight or ISO 27001. These frameworks are excellent – they represent best practice distilled from thousands of organisations’ experiences.
But here’s what many businesses discover: frameworks tell you what good security looks like. They don’t tell you how to get there from where you are now.
Essential Eight, for example, specifies eight critical controls. For each control, it defines three maturity levels. The documentation is comprehensive and freely available.
Yet businesses still struggle to implement it. Why?
- Prioritisation: Which control should you implement first? The answer depends on your current environment, industry, risk profile, and capacity. The framework doesn’t tell you.
- Implementation: The framework says ‘implement application control.’ But how? Which technology? What’s the rollout sequence? How do you handle exceptions? The framework doesn’t specify.
- Verification: You’ve implemented what you think is application control. But is it configured correctly? Will it pass audit? The framework doesn’t verify.
- Evidence: You need to prove compliance. What evidence do auditors expect? When do you collect it? The framework doesn’t guide evidence collection.
- Momentum: Implementation takes months. How do you maintain progress when business priorities shift? The framework doesn’t provide accountability.
Frameworks are maps. But maps don’t navigate for you. You still need a guide who knows the territory.
The One-Off Audit Trap
Recognising they need expert guidance, many businesses commission a security audit or assessment. This seems logical: get an expert to evaluate your security and recommend improvements.
And it works – to a point. You receive a comprehensive report identifying vulnerabilities and recommending controls. For a moment, you feel clarity. Finally, someone has told you what to do.
Then the report arrives. Forty-seven recommendations. Prioritised as ‘Critical,’ ‘High,’ ‘Medium,’ and ‘Low.’ All valid. All important. All overwhelming.
Now you face new questions:
- Should we tackle all the ‘Critical’ items first, even though some are expensive and complex?
- Or should we pick some ‘Quick wins’ to build momentum?
- Six months from now, will these priorities still be right?
- How do we know if we’re implementing them correctly?
- What evidence should we collect to prove we’ve addressed each recommendation?
The audit provided a snapshot. But you need ongoing navigation. Without continued guidance, most audit reports end up filed away, with scattered implementation attempts that never build into coherent security maturity.
One-off audits create what we call ‘Point-in-Time Clarity’—you understand your security posture on the day of the audit. But security is a journey, not a destination. The clarity fades as your environment changes, threats evolve, and you implement controls without verification.
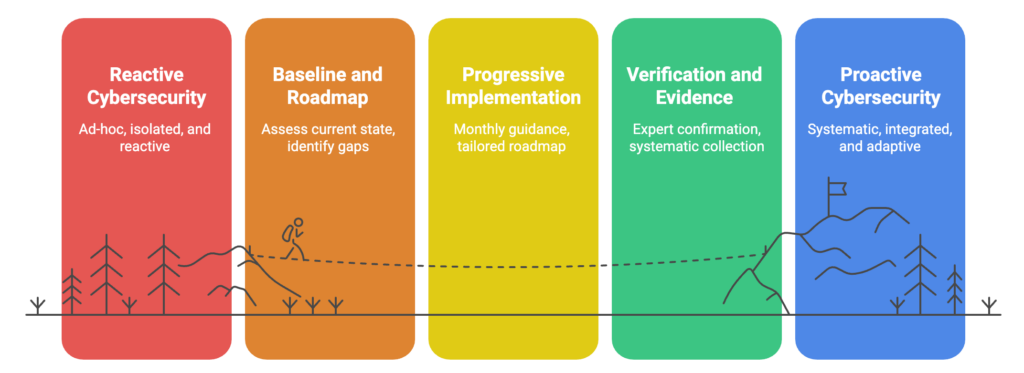
What Strategic Cybersecurity Guidance Actually Looks Like
So if awareness isn’t enough, frameworks need interpretation, IT support handles operations not strategy, and one-off audits leave you stuck—what does work?
Strategic cybersecurity guidance provides what’s missing: ongoing expert advice that helps you make informed decisions month by month.
Here’s what that looks like in practice:
Month 1: Baseline and Roadmap
Assess where you are across recognised frameworks. Identify what you’ve already implemented and where gaps exist. Create a prioritised roadmap based on your specific situation—not generic recommendations, but tailored guidance considering your industry, risk profile, budget, and capacity.
Months 2-12: Progressive Implementation
Monthly meetings guide you through implementing the next controls on your roadmap. Not rushed—at a pace that suits your team’s capacity. Some months you tackle multiple improvements. Other months you focus on embedding one change properly whilst managing other business priorities.
When obstacles arise, you have expert guidance to overcome them. When circumstances change, the roadmap adapts. When new threats emerge, priorities adjust.
Throughout: Verification and Evidence
As you implement each control, expert verification confirms it’s done properly. Evidence is collected systematically—not scrambled together when audit time arrives. When you’re ready for certifications, everything is organised and prepared.
This approach transforms cybersecurity from guesswork into systematic capability building. You’re not wondering if you’re doing the right things—you have ongoing expert confirmation. You’re not stuck implementing an audit report in isolation—you have continuous guidance adapting to your reality.
Moving Beyond Awareness
The businesses that make real security progress aren’t necessarily the most aware of cybersecurity risks. They’re the ones who’ve stopped treating security as a research project and started treating it as a capability to be built, steadily, with expert guidance.
The good news is that the path from awareness to action is more straightforward than the overwhelm suggests. It starts with understanding where you actually stand — not a rough sense of it, but a proper baseline against a recognised framework. From there, the decisions get progressively clearer, because you’re working from facts rather than estimates.
If you’re stuck on the Awareness Plateau, knowing cybersecurity matters but uncertain about what to do next, a baseline assessment is the natural first step.