What Is Cloud Security?
Cloud security is simply a set of policies, controls, procedures, and technologies that work together to protect cloud-based systems, data, and infrastructure. Cloud computing – otherwise referred to as simply “the cloud” – refers to storage, servers, and applications that are hosted online.
But cloud security isn’t the same as cybersecurity – it requires a set of specialised skills and technical knowledge. Our cloud security services are uniquely customised for cloud computing’s unique nuances. However, it addresses both physical and cybersecurity concerns, safeguarding your business from threats such as data breaches, loss, or leakage.
Why is Cloud Security So Important?
Neglecting your cloud security can leave your business vulnerable to a whole host of cyber threats. Enlisting a dedicated IT team to manage your Cloud Security services will ensure that your data and systems are protected.
Here’s how Grassroots IT can assist with your cloud security needs.
Proactive Cybersecurity Defence
As technology evolves, so do cyber threats. These threats can impact your critical systems and data stored in the cloud. By helping you to implement proactive measures, we can prepare your systems to fend off attacks before they happen. Better still, we’re ready 24 hours a day to help out with any urgent cloud security issues. This proactive, always-on approach will reduce downtime for your business.
Expert Guidance
Diving into the world of cloud security can feel overwhelming. But with our tech-savvy professionals and a wealth of experience, we’re here to guide you. Our dedicated team will help you make the smart decisions that keep your cloud data and systems safe and sound.
Increased Productivity
We know that maintaining the integrity and efficiency of your cloud systems and data keeps your business on its feet. Our cloud security solutions will seamlessly integrate with your existing cloud operations, ensuring enhanced protection without any operational disruptions.
Why Choose Grassroots IT?
At Grassroots IT, we understand the intricacies of cloud environments and their unique security challenges. We don’t just have an in-depth understanding of cloud security. We’re focused on tailoring cloud solutions for you that actually suit your business model.
Here’s how partnering with Grassroots IT makes a difference.
The Grassroots IT Difference
With Grassroots IT as your cybersecurity service provider, you’ll benefit from:
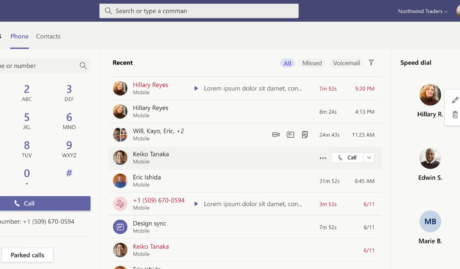
Dedicated Account Manager
Receive a dedicated Account Manager who will understand your needs and offer ongoing and seamless service.
Direct Access To Solution Specialists
Need specialist advice? Tap into our expert guidance instantly with specialists who are trained to help resolve your urgent IT issues either remotely or in person.
Annual Strategy Review & Roadmap
Your IT strategy should be refined regularly according to your changing business goals. Annual reviews hone your tech strategy for success.
Quarterly Alignment Reviews
Regular quarterly check-ins make sure we are aligned with your goals as they evolve. In these reviews, we can make the necessary tweaks to keep your business on track.
Monthly Performance Reporting
The latest insights into your IT performance can empower key decision-makers within your business to make the right decisions when they need.
Extended Helpdesk Hours
Need support? Our dedicated IT Help Desk is available even beyond business hours, providing our clients peace of mind.
24x7 Support
We offer round-the-clock tech support through our IT service desk to offer you and your team assistance at any hour of the day or night.
Australia-Wide Onsite Support
Our IT Support staff are located all across Australia, to ensure we can assist you whenever and wherever you need us.
Dedicated Onboarding Team
We believe that a strong partnership should be defined from the very beginning, which is why we offer you a specialised team to assist with onboarding.
Frequently Asked Questions
How does cloud security differ from traditional IT security?
Cloud security caters specifically to the nuances of cloud computing, addressing challenges related to remote data storage, multi-access points, and virtualised environments.
How often do I need to review my cloud security measures?
Cloud security is dynamic and needs to cater to the changing threats that the modern. At Grassroots IT, we recommend annual reviews or reviews whenever there’s a significant shift in your cloud operations or the overall threat landscape.