The Real Cost of Cybersecurity Decision Paralysis
The most expensive cybersecurity decision most Brisbane businesses make isn’t the wrong product or the wrong vendor. It’s the decision to keep putting off a decision.
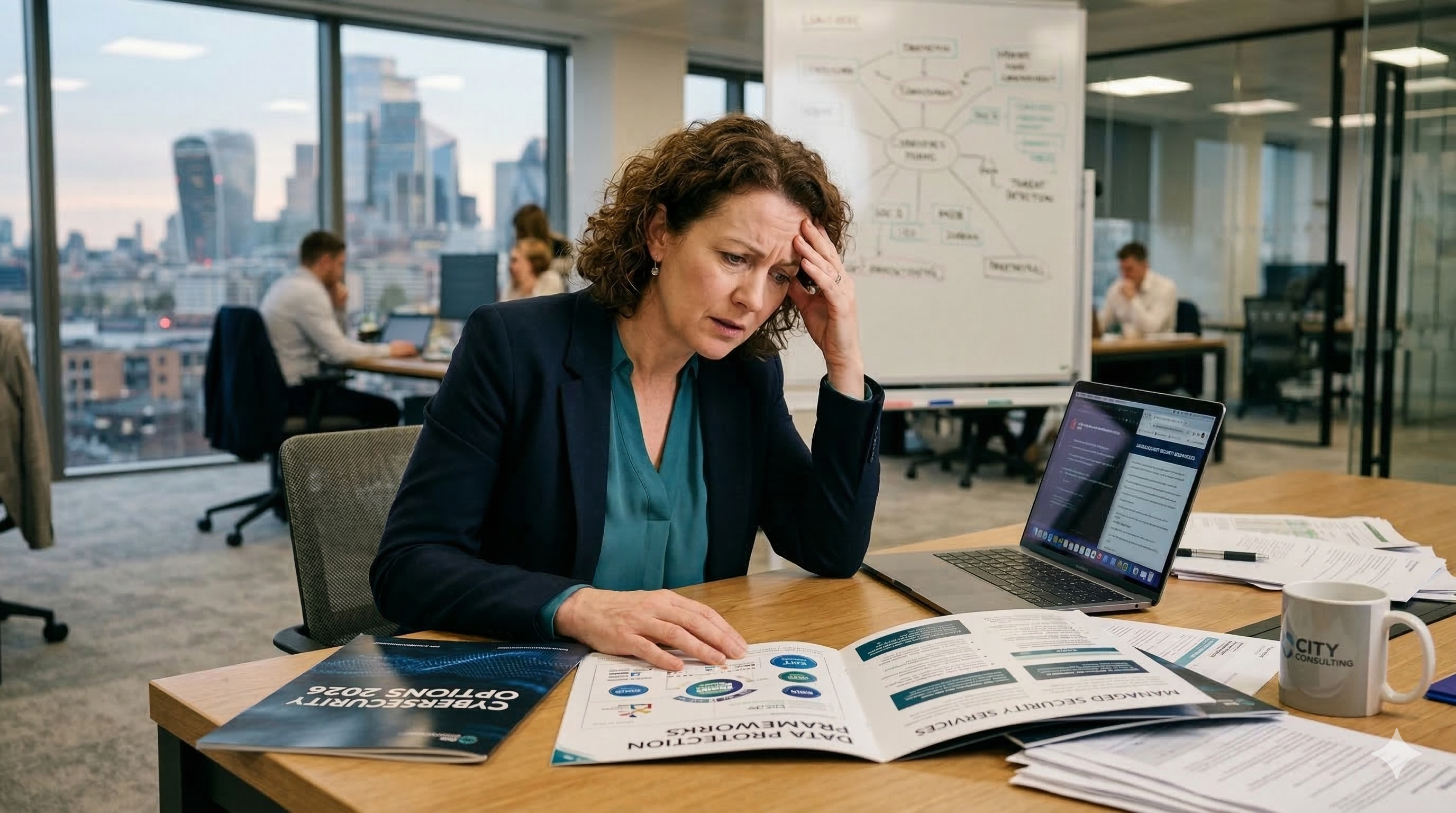
We see this pattern regularly: a business leader knows the security posture needs attention. They’ve probably known for a year or more. So they request a couple of quotes, attend a webinar, bookmark a few articles, and tell themselves they’re being diligent. Meanwhile, the calendar moves forward and the actual risk doesn’t go anywhere.
What looks like prudent deliberation is often something else: decision paralysis. And unlike a bad vendor choice, which you can reverse, paralysis has a way of quietly running up a bill that never appears on an invoice.
Why Smart People Delay Cybersecurity Decisions
Decision paralysis around cybersecurity isn’t irrational. It comes from concerns that are genuinely legitimate.
- Option overwhelm. Every vendor claims their solution is the critical one – firewalls, endpoint protection, security awareness training, vulnerability scanning, penetration testing. Without a trusted framework for prioritising, everything feels equally urgent, which is functionally the same as nothing feeling actionable.
- Budget uncertainty. Quotes range wildly. One consultant quotes $8,000 for an assessment. Another quotes $45,000 for implementation. A third suggests a $120,000 full-time hire. Without context for what your business actually needs, there’s no rational basis for choosing between them.
- Fear of making the wrong call. What if the technology changes? What if the implementation creates a false sense of security? These are reasonable questions, and the stakes do feel high.
- Competing priorities. Cybersecurity sits alongside product development, sales initiatives, and growth investments. It’s easy to tell yourself: we haven’t been breached yet, let’s focus on revenue-generating work first.
All of these concerns are valid. The problem is that whilst you’re carefully weighing them, costs are accumulating in ways that don’t show up until it’s too late to avoid them.
The Hidden Costs of Delayed Decisions
Decision paralysis carries real costs – most of which don’t appear on invoices or in budgets. Here’s what accumulates whilst you delay:
Cost 1: Rising Insurance Premiums
Cyber insurance premiums have increased 50-100% over the past three years. Insurers now require detailed security questionnaires. Without demonstrated maturity – certifications, documented controls, evidence of ongoing management—you’re in the high-risk category.
The cost: For a typical Brisbane SME, the difference between high-risk and demonstrated-maturity premiums can be $5,000-15,000 annually. That’s $60,000-180,000 over three years of delayed security improvements.
Cost 2: Lost Tender Opportunities
More RFPs require security certifications or demonstrated framework compliance. If you can’t tick those boxes, you’re not even shortlisted. Your competitors with Essential Eight or ISO 27001 certifications win by default.
The cost: How many tenders have you declined or not pursued because you knew you couldn’t meet security requirements? Even one missed $100,000+ contract dwarfs most security investments.
Cost 3: Client Confidence Erosion
When clients send security questionnaires and you can’t answer confidently, you’re creating doubt. “We’re working on it” or “That’s on our roadmap” sounds like you’re not taking their data seriously.
The cost: Client relationships are hard to quantify, but erosion is real. Clients who lose confidence in your security posture start evaluating alternatives. By the time they switch, it’s too late to rebuild trust.
Cost 4: Leadership Time Waste
How many hours have you and your leadership team spent researching cybersecurity, getting quotes, attending vendor demonstrations, reviewing proposals, and discussing options without reaching decisions?
The cost: If your leadership team has spent 10 hours monthly for six months researching without deciding, that’s 60 hours. At $200/hour opportunity cost, that’s $12,000 spent on indecision – with nothing to show for it.
Cost 5: Catching Up Is More Expensive
When you finally must improve security – because an insurer demands it, a client requires it, or a regulation mandates it – you’re implementing under pressure. Rushed implementations cost more:
- Premium rates for urgent work
- Mistakes from rushed deployment
- Business disruption from quick changes
- Lack of proper evidence collection
The cost: Urgent security projects typically cost 30-50% more than planned implementations. Plus, quality suffers when you’re racing deadlines.
Cost 6: Regulatory Exposure
Privacy and security regulations are tightening globally. The Australian Privacy Act amendments, mandatory breach notification requirements, and industry-specific regulations all increase compliance obligations.
Businesses that haven’t built security maturity face regulatory risk. When breaches occur – and statistically, they will – demonstrable security efforts influence both regulatory response and public perception.
The cost: Regulatory fines, legal fees, remediation costs, and reputational damage. For Australian businesses, data breach costs on average $4.26 million according to IBM’s 2024 Cost of a Data Breach Report.
The Opportunity Cost of Inaction
Beyond direct costs, decision paralysis carries opportunity costs—benefits you forgo by not improving security:
Competitive Advantage Lost
Security maturity is becoming a competitive differentiator. Businesses that can demonstrate Essential Eight compliance or ISO 27001 certification win contracts against competitors who can’t. They command premium pricing because clients value demonstrated security.
Whilst you delay, competitors are building this advantage.
Strategic Clarity Missed
Businesses with strong security posture make better strategic decisions. They can confidently pursue cloud migrations, enable remote work, adopt new technologies, and expand into regulated industries—all opportunities that require security confidence.
Decision paralysis on security creates decision paralysis on strategy.
Peace of Mind Deferred
There’s a psychological cost to ongoing uncertainty. Business leaders who aren’t confident in their security spend mental energy worrying. Every news story about a breach triggers anxiety. Every client questionnaire creates stress.
Confidence in your security posture frees mental bandwidth for growth activities.
What Breaks the Paralysis
Understanding the costs of inaction helps, but it doesn’t answer the underlying question: where do you actually start?
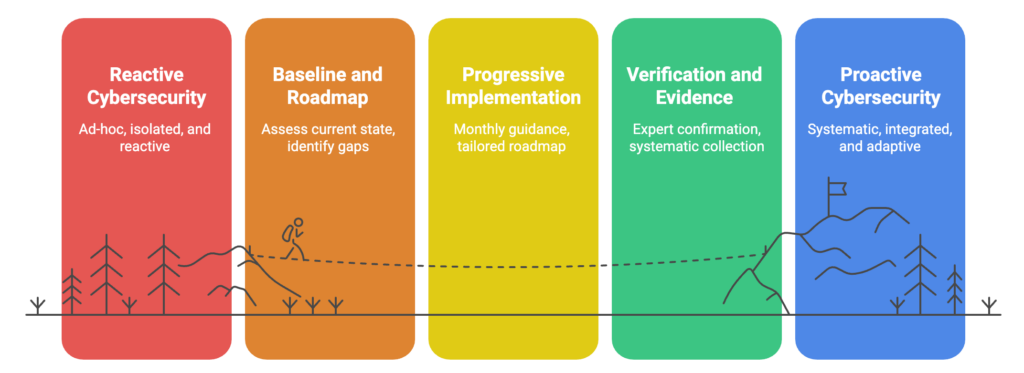
In our experience, what breaks the cycle isn’t more information – it’s structure. Most of the businesses we work with that have been stuck in research mode for months aren’t lacking data; they’re lacking a decision-making framework and someone they trust to guide them through it.
Trusted guidance matters more than most people realise. When you’re evaluating vendors who all have an interest in the outcome, you can’t get unbiased prioritisation. What actually moves things forward is an adviser who can look at your specific situation and say: given where you are, here’s what matters first, and here’s what can wait.
Recognised frameworks like Essential Eight and SMB1001 are genuinely useful here — not because they make the decision for you, but because they dramatically reduce the number of decisions you need to make. Instead of evaluating every possible security improvement against every other, you’re working through a structured set of proven controls that insurers, clients, and regulators already recognise. The scope becomes manageable.
Staged investment helps too. You don’t need to commit to everything at once, and framing security improvement as a 12-month journey rather than a single project changes the calculus entirely.
But the thing that matters most – and what we see makes the biggest difference – is simply a clear starting point. Most businesses delay because they don’t know where they currently stand. A baseline assessment against a recognised framework gives you that. Once you know the gap between where you are and where you need to be, the next decision becomes obvious rather than overwhelming.
The Cost-Benefit Reality
Let’s put the costs of inaction into perspective with actual numbers:

Meanwhile, strategic cybersecurity investment typically ranges from $30,000-60,000 annually for comprehensive guidance and implementation.
The question isn’t whether you can afford to invest in cybersecurity. It’s whether you can afford to keep delaying.
Breaking Free From Paralysis
If you recognise your business in any of this, the path forward is simpler than the research phase has probably made it feel.
The gap between where most businesses are and where they need to be is almost always smaller than the paralysis suggests. And the businesses that finally move forward consistently say the same thing: the relief of having a concrete plan, rather than an open-ended research project, was immediate. The hard part wasn’t the work. It was making the first move.
Start by acknowledging that inaction has a cost. Then get a baseline. From there, the decisions get progressively easier, because you’re working from facts rather than estimates.
If you’d like to understand where you currently stand, a baseline assessment against Essential Eight or SMB1001 is the natural first step.
The Bottom Line
The businesses that make real security progress aren’t necessarily the ones with the biggest budgets. They’re the ones who’ve recognised that structured action, even imperfect action, beats indefinite research.
If you’ve been stuck in cybersecurity decision paralysis, calculate what delay is actually costing you. The number might surprise you, and it might be exactly what finally moves things forward.
Ready to move from research to action? The first step is understanding where you currently stand. A baseline security assessment can break decision paralysis by giving you concrete starting point. Contact us today to discuss your current cybersecurity posture and next best steps forward.
Why Knowing Cybersecurity Is Important Isn't Enough
Every business leader knows cybersecurity matters. Yet most still struggle to make meaningful progress. The problem isn’t awareness – it’s knowing what to do next.
Most Brisbane business leaders we speak to can articulate the cybersecurity risks their business faces. They’ve read the breach headlines. They know their clients are asking harder questions. They understand the insurance market has changed.
Awareness is no longer the problem.
What most businesses haven’t solved is what comes after awareness: making confident, informed decisions about what to actually do. Ask a business leader what specifically they’re working on, how they decided those were the right priorities, and how they measure progress and that’s usually where the certainty evaporates.
The Awareness Plateau
Over the past decade, cybersecurity awareness has skyrocketed. Businesses understand the risks. They’ve read the headlines about ransomware attacks. They know client data needs protecting. They’re aware insurance companies are asking harder questions.
Awareness is no longer the problem.
The problem is what comes after awareness: making informed decisions about what to actually do.
Most businesses get stuck on what we call the Awareness Plateau. They know cybersecurity matters, but without expertise to guide decisions, they’re left guessing:
- Should we invest in a new firewall or focus on user training first?
- Is multi-factor authentication more urgent than application control?
- Should we commission another security audit or actually implement the last one?
- How do we know if we’re making real progress or just ticking boxes?
These aren’t questions about whether cybersecurity matters. They’re questions about how to make progress when you don’t have internal expertise to guide the journey.

The Decision Dilemma
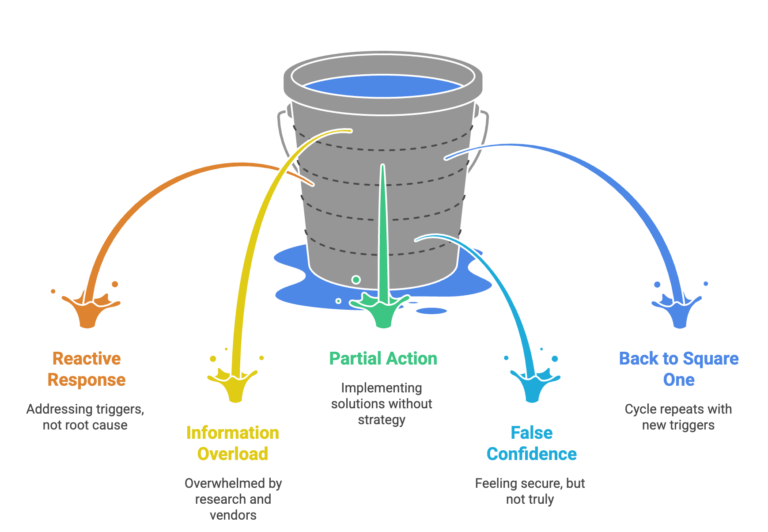
Here’s what the decision-making process looks like for most businesses without dedicated cybersecurity expertise, and it tends to follow a familiar pattern.
Something triggers concern: a client questionnaire, an insurance renewal, a news story about a breach that hits close to home. So the research begins. Google returns millions of results, every vendor claims their solution is the critical one, and the more you read, the more overwhelming it becomes.
Eventually, something gets implemented, usually whatever seemed most urgent or was recommended by the last person you spoke to. A firewall upgrade, a security audit, a new backup solution. For a while, it feels like progress. The immediate concern is addressed and security feels handled.
Then, six months later, another trigger arrives. A different client questionnaire. A new insurance requirement. And the realisation sets in: you’re still not confident about your overall security posture. You still don’t know if you’re focusing on the right things. You’re back to square one.
This cycle repeats because the underlying problem hasn’t changed: security decisions are being made without security expertise to guide them.
Why General IT Support Isn't Enough
Many businesses assume their IT support provider handles cybersecurity. And in a sense, they do – but there’s a critical distinction most people miss.
Your IT support keeps your environment secure operationally. They patch systems, configure firewalls, manage antivirus, respond to incidents, and maintain security configurations. This is essential – it’s your security foundation.
But operational security and strategic security are different capabilities:
Operational Security (What IT Support Provides):
- Keeping systems patched and updated
- Maintaining secure configurations
- Responding to security incidents
- Implementing technologies when requested
- Following best practices
Strategic Security (The Missing Layer):
- Assessing current maturity against recognised frameworks
- Prioritising improvements based on risk and business context
- Building systematic capability over time
- Collecting evidence for certifications and audits
- Demonstrating maturity to insurers, clients, and regulators
Think of it this way: operational security keeps your house locked and the alarm working. Strategic security ensures you’re protecting the right rooms, meeting building codes, and can prove it to your insurer.
You need both. But most businesses only have the operational layer.
The Framework Gap
When businesses do seek strategic guidance, they often turn to security frameworks like Essential Eight or ISO 27001. These frameworks are excellent – they represent best practice distilled from thousands of organisations’ experiences.
But here’s what many businesses discover: frameworks tell you what good security looks like. They don’t tell you how to get there from where you are now.
Essential Eight, for example, specifies eight critical controls. For each control, it defines three maturity levels. The documentation is comprehensive and freely available.
Yet businesses still struggle to implement it. Why?
- Prioritisation: Which control should you implement first? The answer depends on your current environment, industry, risk profile, and capacity. The framework doesn’t tell you.
- Implementation: The framework says ‘implement application control.’ But how? Which technology? What’s the rollout sequence? How do you handle exceptions? The framework doesn’t specify.
- Verification: You’ve implemented what you think is application control. But is it configured correctly? Will it pass audit? The framework doesn’t verify.
- Evidence: You need to prove compliance. What evidence do auditors expect? When do you collect it? The framework doesn’t guide evidence collection.
- Momentum: Implementation takes months. How do you maintain progress when business priorities shift? The framework doesn’t provide accountability.
Frameworks are maps. But maps don’t navigate for you. You still need a guide who knows the territory.
The One-Off Audit Trap
Recognising they need expert guidance, many businesses commission a security audit or assessment. This seems logical: get an expert to evaluate your security and recommend improvements.
And it works – to a point. You receive a comprehensive report identifying vulnerabilities and recommending controls. For a moment, you feel clarity. Finally, someone has told you what to do.
Then the report arrives. Forty-seven recommendations. Prioritised as ‘Critical,’ ‘High,’ ‘Medium,’ and ‘Low.’ All valid. All important. All overwhelming.
Now you face new questions:
- Should we tackle all the ‘Critical’ items first, even though some are expensive and complex?
- Or should we pick some ‘Quick wins’ to build momentum?
- Six months from now, will these priorities still be right?
- How do we know if we’re implementing them correctly?
- What evidence should we collect to prove we’ve addressed each recommendation?
The audit provided a snapshot. But you need ongoing navigation. Without continued guidance, most audit reports end up filed away, with scattered implementation attempts that never build into coherent security maturity.
One-off audits create what we call ‘Point-in-Time Clarity’—you understand your security posture on the day of the audit. But security is a journey, not a destination. The clarity fades as your environment changes, threats evolve, and you implement controls without verification.
What Strategic Cybersecurity Guidance Actually Looks Like
So if awareness isn’t enough, frameworks need interpretation, IT support handles operations not strategy, and one-off audits leave you stuck—what does work?
Strategic cybersecurity guidance provides what’s missing: ongoing expert advice that helps you make informed decisions month by month.
Here’s what that looks like in practice:
Month 1: Baseline and Roadmap
Assess where you are across recognised frameworks. Identify what you’ve already implemented and where gaps exist. Create a prioritised roadmap based on your specific situation—not generic recommendations, but tailored guidance considering your industry, risk profile, budget, and capacity.
Months 2-12: Progressive Implementation
Monthly meetings guide you through implementing the next controls on your roadmap. Not rushed—at a pace that suits your team’s capacity. Some months you tackle multiple improvements. Other months you focus on embedding one change properly whilst managing other business priorities.
When obstacles arise, you have expert guidance to overcome them. When circumstances change, the roadmap adapts. When new threats emerge, priorities adjust.
Throughout: Verification and Evidence
As you implement each control, expert verification confirms it’s done properly. Evidence is collected systematically—not scrambled together when audit time arrives. When you’re ready for certifications, everything is organised and prepared.
This approach transforms cybersecurity from guesswork into systematic capability building. You’re not wondering if you’re doing the right things—you have ongoing expert confirmation. You’re not stuck implementing an audit report in isolation—you have continuous guidance adapting to your reality.
Moving Beyond Awareness
The businesses that make real security progress aren’t necessarily the most aware of cybersecurity risks. They’re the ones who’ve stopped treating security as a research project and started treating it as a capability to be built, steadily, with expert guidance.
The good news is that the path from awareness to action is more straightforward than the overwhelm suggests. It starts with understanding where you actually stand — not a rough sense of it, but a proper baseline against a recognised framework. From there, the decisions get progressively clearer, because you’re working from facts rather than estimates.
If you’re stuck on the Awareness Plateau, knowing cybersecurity matters but uncertain about what to do next, a baseline assessment is the natural first step.
The Reality Check Every SMB Leader Faces
You open your cyber insurance renewal and see a 40% premium increase. Again. The fine print highlights “required security controls” and references frameworks you’ve never heard of. Meanwhile, one of your key clients just sent a vendor security questionnaire asking about your “cybersecurity maturity framework.”
This isn’t just paperwork, it’s the new cost of doing business. Australian SMBs are discovering that basic antivirus and backups no longer satisfy insurers, clients, or compliance requirements. The challenge isn’t just implementing better security; it’s finding a structured approach that delivers enterprise-level protection without enterprise-level complexity. Referencing a cybersecurity compliance checklist can streamline this process. This highlights the growing importance of cybersecurity for SMBs.
Modern cybersecurity requires layered defences, documented processes, continuous monitoring, and measurable outcomes. Yet most security frameworks were designed for large enterprises with dedicated security teams and unlimited budgets.
That’s exactly why SMB1001 exists—the cybersecurity framework purpose-built for businesses with 5-200 employees.
The Business Case for Structured Security
Before diving into technical details, let’s address the financial reality. Cybersecurity incidents don’t just cost money. They disrupt operations, damage client relationships, and can permanently impact your reputation. Meanwhile, cyber insurance premiums continue rising while coverage becomes more restrictive.
What we’re seeing across our client base is clear: businesses with documented security frameworks experience faster vendor approval processes, reduced insurance scrutiny, and access to opportunities that were previously out of reach.
The revenue opportunity is significant. Enterprise clients increasingly require vendor security assessments before engagement, and demonstrable alignment with the SMB1001 standard satisfies most security questionnaires. This opens doors to contracts and partnerships that security-conscious organisations simply won’t consider without proper documentation. This highlights the growing importance of cybersecurity for SMBs.
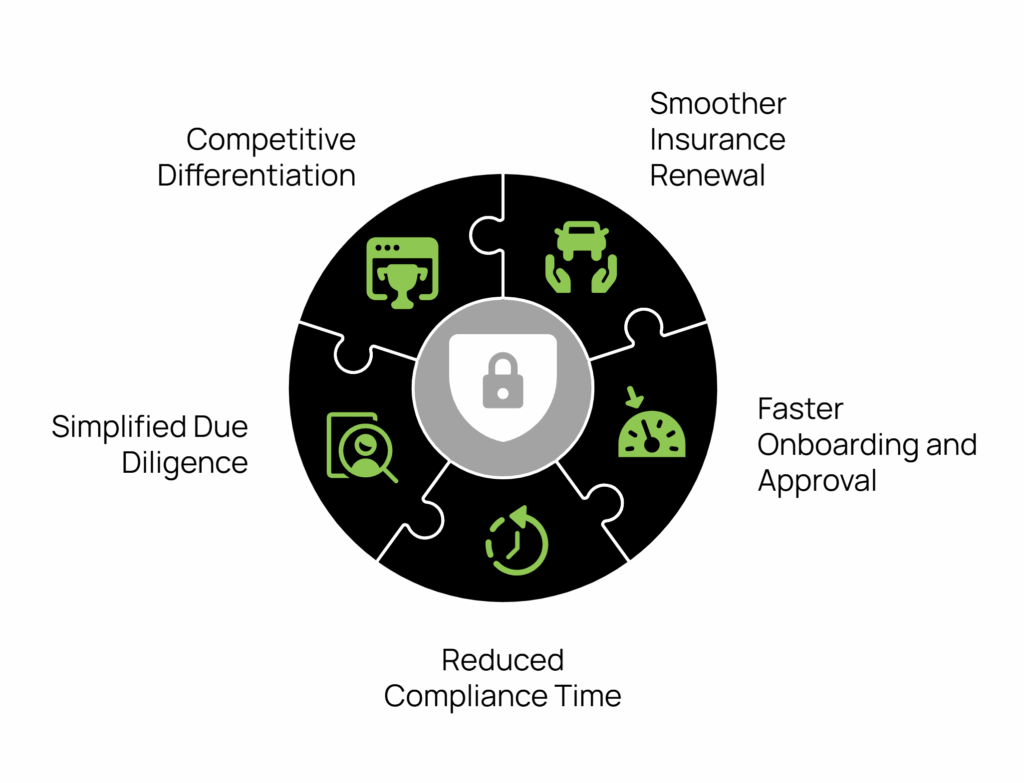
Structured security implementation delivers measurable business benefits:
- Smoother insurance renewal processes with better terms
- Faster vendor onboarding and client approval cycles
- Reduced time spent on security questionnaires and compliance preparation
- Simplified due diligence for partnerships and potential acquisitions
- Clear competitive differentiation in security-conscious markets
What Makes SMB1001 Different
Established cybersecurity frameworks like ISO 27001 and NIST are excellent, comprehensive standards that have proven their value across thousands of organisations worldwide. The challenge? These frameworks were designed for enterprises with dedicated security teams, substantial budgets, and complex organisational structures.
“SMB1001 takes the proven security principles from these established frameworks and adapts them specifically for smaller organisations—making enterprise-level cybersecurity both practical and achievable for growing businesses.”
The SMB1001 framework delivers this practical approach through four key characteristics that address the specific challenges growing businesses face:
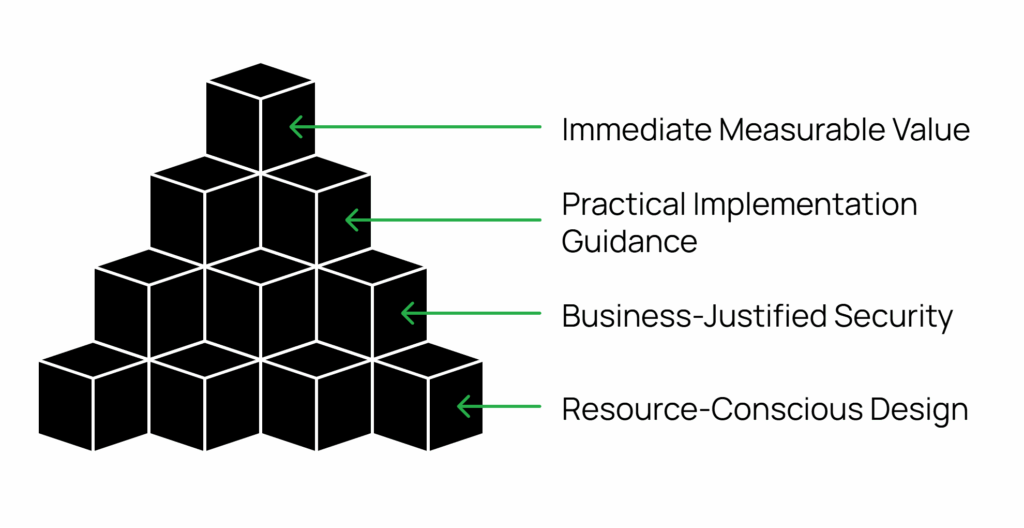
Resource-Conscious Design: Every control is evaluated against implementation cost and ongoing maintenance requirements. No recommendations require dedicated security staff or enterprise-grade budgets.
Business-Justified Security: Rather than generic best practices, each security measure directly ties to protecting your revenue, reputation, and operational continuity. This approach ensures businesses understand not just what to implement, but why it matters to their specific business model.
Practical Implementation Guidance: Step-by-step processes your existing team can follow without specialised cybersecurity expertise, supported by templates, checklists, and decision trees that eliminate guesswork.
Immediate Measurable Value: Quick wins and visible improvements establish momentum while building toward comprehensive protection that scales with your growth.
The Three-Tier Approach That Scales with Your Business
Bronze Level: Essential Security Foundation
Perfect for establishing baseline protection and meeting basic compliance requirements. Achieving Bronze-level alignment addresses the most common attack vectors and can typically be accomplished within 6-8 weeks. Referencing a cybersecurity compliance checklist can streamline this process.
Core implementations:
- Complete asset inventory and management systems
- Strong authentication policies with multi-factor authentication
- Documented incident response procedures
- Regular security awareness training program
- Reliable backup and recovery systems
Business outcome: Satisfies most insurance and basic client security requirements while dramatically reducing your exposure to common attack vectors.
Silver Level: Advanced Protection and Monitoring
Designed for businesses handling sensitive data or operating in regulated industries. Silver builds advanced capabilities on your Bronze foundation over an additional 8-10 weeks.
Enhanced capabilities:
- Advanced threat detection with automated response
- Network segmentation protecting critical systems
- Regular vulnerability assessments with remediation tracking
- Comprehensive backup strategy with tested recovery procedures
- Third-party vendor security assessments
Business outcome: Documented security controls needed for enterprise client contracts while significantly reducing successful cyberattack risk.
Gold Level: Cyber Resilience as Strategic Asset
Full cyber resilience for organisations viewing cybersecurity as a competitive advantage. Gold-level organisations often see security transform from cost centre to revenue driver.
Advanced capabilities:
- Continuous security monitoring with 24/7 threat response
- Business continuity planning with regular testing
- Supply chain security management
- Organisation-wide security culture integration
- Regular independent security assessments
Business outcome: Win contracts specifically because of your security posture. Access previously restricted markets where security certification is mandatory.
Your Implementation Path Forward
Rather than overwhelming you with detailed project plans, SMB1001 focuses on sustainable progress through clear phases:
Foundation Phase: Comprehensive security assessment establishes your baseline and identifies quick wins. Basic access controls and password policies provide immediate risk reduction.
Core Controls Phase: Deploy essential systems including asset management, incident response procedures, and reliable backups. Complete initial staff security training and document key policies.
Assessment Phase: Evaluate your implementation against Bronze-level requirements and address any remaining gaps. Establish a baseline for potential advancement to silver or gold levels.
Why Acting Now Creates Competitive Advantage
The cybersecurity landscape continues evolving rapidly. Regulatory requirements expand, insurance standards rise, and client expectations grow more sophisticated. The organisations implementing structured cybersecurity frameworks today position themselves as trusted partners for tomorrow’s opportunities. These are part of the evolving cyber insurance requirements.
More critically, cyber threats evolve daily. Every day without proper security controls exponentially increases your exposure to incidents that could devastate operations and reputation.
SMB1001 cybersecurity framework isn’t about achieving perfect security overnight, it’s about building practical, sustainable cybersecurity that fits your business reality. Whether you need Bronze-level alignment to satisfy current requirements or Gold-level maturity to pursue enterprise opportunities, the framework provides a clear, achievable path forward.
Take Your First Step Toward Strategic Security
The question isn’t whether you’ll eventually need structured cybersecurity, it’s whether you’ll implement it proactively or be forced into it reactively after an incident.
Our SMB1001 Gap Assessment Audit identifies your current security posture and maps your most efficient path to certification. Get clarity on your cybersecurity journey with a practical evaluation of your existing controls and priority improvements.
Transform cybersecurity from a compliance burden into a strategic business asset. Your future self will thank you.
More and more Australian organisations are discovering the strategic advantage of ISO 27001 certification. It’s exciting to see businesses of all sizes embracing this globally recognised security standard, opening doors to new partnerships and market opportunities. What was traditionally the domain of enterprise organisations has evolved into a powerful business enabler for growing companies across the country.
What’s ISO 27001 All About?
Strip away the fancy language, and ISO 27001 is simply an internationally recognised way to prove you’re serious about protecting information. While it might sound complex, at its heart it’s about having a systematic approach to keeping customer data safe, protecting your business from cyber threats, managing access to information, and being prepared when things go wrong. Think of it like a driver’s licence for information security – it proves you know what you’re doing and can be trusted to handle sensitive information properly.
Meeting ISO Requirements with Microsoft 365
The good news is that Microsoft 365 already includes a range of features that can directly support your journey to ISO 27001 compliance. Let’s look at exactly how you can use Microsoft 365 features to meet specific ISO requirements. Here’s your practical guide to ticking those ISO boxes using tools you already have.
How to Meet It with Microsoft 365
User Access Management
What ISO Requires
The standard demands formal processes for managing user access throughout the entire employee lifecycle. This control exists because inappropriate access rights are a major security risk – think ex-employees with active accounts, or staff with more system access than they need. ISO wants to see that you’re actively managing these risks through formal processes and regular reviews. You need a systematic way to grant, modify, and revoke access based on people’s roles, ensuring everyone has exactly what they need to do their job – nothing more, nothing less.
Real-world example
- When Sarah from Accounts leaves, all her access needs to be removed within 24 hours
- When Jim moves from Support to Sales, his system access needs to change to match his new role
- Every quarter, managers need to confirm their team members still need their current access levels
- When Dave from IT needs admin access to fix an urgent issue, it should be time-limited and logged
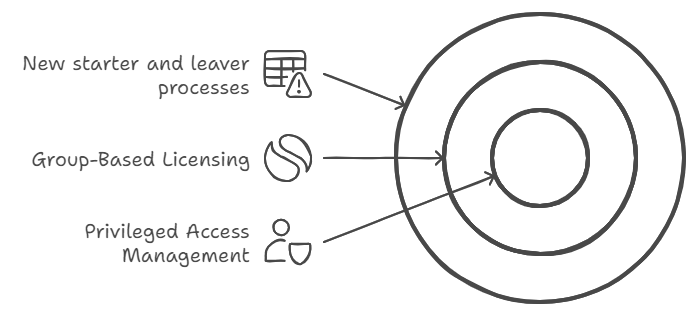
1. For new starter and leaver processes:
- Set up automated workflows in Azure AD: When HR marks an employee as terminated, their accounts are automatically disabled
- Configure group-based licensing: New sales staff automatically get Salesforce access, while marketing gets Adobe Creative Suite
- Use access reviews: Managers get quarterly emails to verify their reports still need access to sensitive data
- Enable Microsoft Groups expiration: Teams/SharePoint access automatically expires if not renewed
2. For privileged access management:
- Set up just-in-time access: IT staff request admin rights for 2 hours to perform maintenance
- Configure approval workflows: Senior IT approval required for global admin access
- Enable session recording: All admin activities in sensitive systems are logged
Authentication Controls
What ISO Requires
You need to prove you’re properly controlling system access. This requirement recognises that passwords alone aren’t enough anymore. ISO wants evidence that you’re using modern authentication methods to verify users’ identities, especially when accessing sensitive information or systems. It’s about making sure that even if someone gets hold of a password, they can’t automatically access your systems. The standard also emphasises the importance of protecting access information – like making sure password rules are strong enough and that you can detect and block suspicious login attempts.
Real-world examples:
- Jane shouldn’t be able to log in with just a password when accessing payroll data from home
- Failed password attempts should lock an account after 5 tries
- If Bob’s session is idle for 15 minutes, he should be logged out
- When Alice tries to log in from an unusual location, extra verification should be required
How to Meet It with Microsoft 365
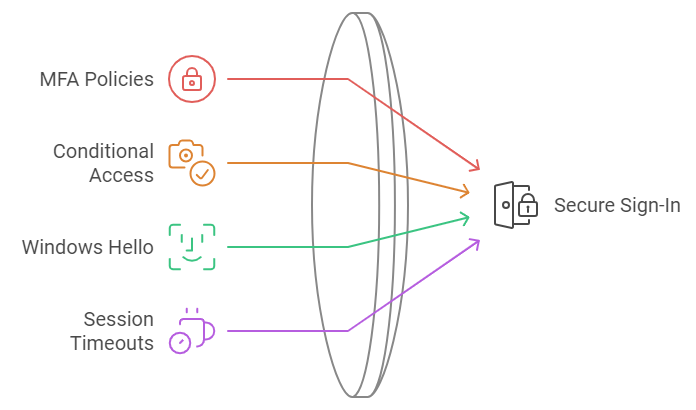
1. For secure sign-in:
- Configure MFA policies: Force additional verification for all remote access
- Set up Conditional Access: Require managed devices for accessing customer data
- Enable Windows Hello: Replace passwords with biometric login
- Configure session timeouts: Auto-logout after 15 minutes of inactivity
Information Classification
What ISO Requires
You must show that sensitive information is properly identified and protected. This control recognises that not all information needs the same level of protection – your marketing brochure doesn’t need the same security as your customer credit card details. ISO requires you to think through what types of information you handle, how sensitive each type is, and what protection it needs. Then you need to show that you’ve got systems in place to consistently identify and protect information based on its sensitivity level.
Real-world examples:
- Customer credit card details need the highest level of protection
- Internal project documents shouldn’t be shareable outside the company
- HR documents should only be accessible by the HR team
- Marketing materials can be widely shared but not modified by everyone
How to Meet It with Microsoft 365
1. For automatic classification:
- Create sensitivity labels: “Confidential-Finance”, “Internal-Only”, “Public”
- Configure auto-labelling: Documents with credit card numbers automatically marked as “Confidential”
- Set up visual markers: Confidential documents get a red header saying “Internal Use Only”
2. For information handling:
- Enable encryption: “Confidential” documents can only be opened by approved users
- Set up DLP: Block sharing of documents containing tax file numbers
- Configure SharePoint permissions: HR site only accessible by HR team members
Cryptographic Controls
What ISO Requires
Sensitive data must be properly encrypted. This requirement goes beyond just turning on encryption – ISO wants to see that you’ve thought through when and where encryption is needed, and that you’re managing it properly. This includes having formal policies about what needs to be encrypted, managing encryption keys securely, and making sure your encryption methods are strong enough for the sensitivity of the data you’re protecting. It’s about ensuring that if someone does get unauthorized access to your systems, they still can’t read your sensitive data.
Real-world examples:
- Client contracts must be encrypted when stored
- Financial reports being emailed to the board need encryption
- Mobile devices with company data must be encrypted
- Backup files need to be encrypted before going to cloud storage
How to Meet It with Microsoft 365

1. For data at rest:
- Enable BitLocker: All laptop drives automatically encrypted
- Configure SharePoint encryption: All documents encrypted with unique keys
- Set up Exchange mailbox encryption: Emails encrypted by default
2. For data in transit:
- Enable TLS: All email communications encrypted in transit
- Configure secure external sharing: Client portal access using encrypted connections
- Set up encrypted backup: Automatic encryption before cloud backup
Logging and Monitoring
What ISO Requires
ISO needs you to prove you’re actively monitoring your systems. This means having systems in place to detect, capture, and investigate security events and user activity. It’s not just about recording what happens – you need to show that you’re actively reviewing these records and can spot potential security incidents quickly. Think of it like CCTV for your IT systems – it needs to be recording, but someone also needs to be watching the monitors.
Real-world examples:
- All admin actions in key systems need to be logged and reviewable
- Failed login attempts need to be monitored and investigated
- File access patterns need to be tracked to spot unusual behaviour
- System changes need to be logged and attributable to specific users
How to Meet It with Microsoft 365
1. For audit logging:
- Enable Unified Audit Logging in Security & Compliance
- Configure alert policies for sensitive actions
- Set up log retention policies for compliance
2. For security monitoring:
- Enable Microsoft Defender for Cloud Apps
- Configure alert policies for suspicious activities
- Set up automated incident reporting
Communications Security
What ISO Requires
Information needs to be protected whenever it’s being shared or moved around. This control focuses on keeping data safe when it’s in transit between systems or being shared with external parties. It’s about making sure sensitive information can’t be intercepted or tampered with when it’s moving between point A and point B, whether that’s within your network or out to external partners.
Real-world examples:
- Customer data being shared with partners needs encryption
- Confidential emails need to be protected from interception
- File transfers between systems need to be secure
- External collaboration needs to be controlled and monitored
How to Meet It with Microsoft 365
1. For email security:
- Enable Exchange Online Protection
- Configure anti-phishing policies
- Set up Safe Attachments and Safe Links
2. For secure file sharing:
- Configure SharePoint sharing policies
- Enable Teams external access controls
- Set up secure guest access policies
The Bottom Line
Getting ISO 27001 certified doesn’t mean buying new security tools. Microsoft 365 includes powerful features that map directly to ISO requirements – you just need to know what to turn on and how to configure it.
Need help setting up these controls or mapping them to your ISO requirements? That’s what we do. Let’s talk about getting your Microsoft 365 environment ISO-ready.
For small to medium-sized businesses, Microsoft 365 Business Premium offers a robust suite of productivity tools coupled with advanced security features. However, many organisations are not taking full advantage of the security capabilities included in their subscription. In this post, we’ll explore the key security features of Microsoft 365 Business Premium and how you can leverage them to protect your business.
Understanding Microsoft 365 Business Premium
Microsoft 365 Business Premium is more than just a productivity suite—it’s a comprehensive solution that combines the familiar Office applications with advanced security and device management capabilities. This license tier is often considered the “sweet spot” for small to medium-sized businesses, offering enterprise-grade features at a fraction of the cost.
Key Security Features in Microsoft 365 Business Premium
Let’s dive into the security features that come standard with your Business Premium license:
1. Microsoft Defender for Office 365 (Plan 1)
Microsoft Defender for Office 365 is a cloud-based email filtering service that helps protect your organisation against advanced threats like phishing and zero-day malware.
Key components include:
- Safe Links: This feature provides time-of-click verification of URLs in emails and Office documents. It helps protect your organisation by checking web addresses against a list of known malicious links.
- Safe Attachments: This feature checks email attachments for malicious content. It opens attachments in a virtual environment to detect malicious behaviour before delivering the email.
- Anti-phishing protection: Advanced machine learning models and impersonation detection help protect your users from phishing attacks.
Pro Tip: These features aren’t necessarily enabled by default, so make sure to activate them to take full advantage of their capabilities.
2. Intune Mobile Device Management
Intune is Microsoft’s mobile device management (MDM) and mobile application management (MAM) platform. It allows you to manage both company-owned and personal devices used to access company data.
Key benefits include:
- Enforce device-level security policies (e.g., requiring a PIN to unlock the device)
- Selectively wipe company data from lost or stolen devices
- Manage and deploy apps to devices
Pro Tip: Start with basic policies like requiring a device PIN and the ability to remotely wipe company data. Gradually introduce more advanced policies as your team becomes comfortable with the system.
3. Azure Information Protection (AIP)
AIP helps you classify, label, and protect sensitive information. It can automatically detect sensitive data types (like credit card numbers or health information) and apply appropriate protections.
Key features:
- Prevent sensitive information from being shared inappropriately
- Track and control how protected information is used
Pro Tip: Begin by identifying your most sensitive data types and creating policies to protect them. Educate your users on the importance of data classification and how to use the AIP tools effectively.
4. Multi-Factor Authentication (MFA)
MFA is one of the most effective ways to protect against unauthorised access. It requires users to provide two or more verification factors to gain access to a resource, significantly reducing the risk of compromised accounts.
Pro Tip: Implement MFA for all users, starting with administrators and gradually rolling out to all staff. Consider using the Microsoft Authenticator app for a seamless user experience.
5. Conditional Access Policies
Conditional Access allows you to control access to your resources based on specific conditions. You can create policies that grant or restrict access based on factors like user location, device status, and detected risk level.
Key use cases:
- Block access from countries where your business doesn’t operate
- Require MFA for access to sensitive applications
- Ensure only managed and compliant devices can access company resources
Pro Tip: Start with a few critical policies and gradually expand. Always test new policies in a limited pilot before full deployment.
6. Exchange Online Archiving
While primarily a compliance feature, Exchange Online Archiving contributes to security by helping you retain and protect important email data. It provides users with an archive mailbox for storing old email messages.
Key benefits:
- Automatic movement of old emails to the archive based on policies
- eDiscovery capabilities for legal or compliance needs
- Retention policies to ensure important data isn’t accidentally deleted
Pro Tip: Set up retention policies that align with your industry regulations and business needs. Train users on how to access and use their archive mailboxes effectively.
Case Study: Small Business Success with M365 Business Premium Security
One of our clients, a local mining company with 70 employees was struggling with security concerns, particularly around protecting client financial data. By implementing Microsoft 365 Business Premium and fully leveraging its robust security features, the company saw significant improvements:
- 90% reduction in phishing emails reaching user inboxes
- Zero data breaches in the 6 months following implementation
- Improved ability to meet industry compliance requirements
- Increased employee productivity due to reduced downtime from security incidents
- Streamlined device management using Intune Compliance and configuration policies
- Standardised app deployment to all users leveraging Intune app deployment policies.
- Improved access controls using Conditional Access policies to for Geo Location, User risk and MFA
The firm faced initial challenges with user adoption, particularly around MFA and Geo Location policies. However, with a comprehensive user training campaign, they achieved full adoption within three months.
Conclusion
Microsoft 365 Business Premium offers a wealth of security features that can significantly enhance your organisation’s cybersecurity posture. By fully leveraging these tools, you can protect your business against a wide range of threats while also improving productivity and compliance.
Remember, cybersecurity is not a one-time effort but an ongoing process. Regularly review and update your security measures to stay ahead of evolving threats.
How Grassroots IT Can Help
At Grassroots IT, we specialise in helping businesses make the most of their Microsoft 365 investments. Our team of experts can:
- Assess your current security posture and identify areas for improvement
- Develop a customised implementation plan for M365 Business Premium security features
- Provide user training to ensure smooth adoption of new security measures
- Offer ongoing support and optimisation of your Microsoft 365 environment
Don’t leave your business vulnerable. Contact us today for a consultation, and let’s explore how we can enhance your cybersecurity with Microsoft 365 Business Premium.
Traditional security measures, while still important, are no longer sufficient to protect your organisation from sophisticated attacks. Enter Conditional Access Policies: a powerful tool in the Microsoft 365 suite that can significantly enhance your cybersecurity posture. In this post, we’ll explore how these policies work and why they are becoming an essential component of modern cybersecurity strategies.
What are Conditional Access Policies?
Conditional Access Policies are a feature of Microsoft 365 that allows you to control access to your organisation’s resources based on specific conditions. Think of them as smart gatekeepers for your digital assets. Instead of a simple “yes” or “no” to access requests, these policies consider various factors before granting access, such as:
- Who is requesting access?
- Where are they accessing from?
- What device are they using?
- What level of risk is associated with the access request?
By evaluating these factors in real-time, Conditional Access Policies can make nuanced decisions about whether to grant access, deny access, or require additional verification.
Current State of Cybersecurity
It’s not hyperbole to say that cybersecurity threats are growing exponentially, so before we dive deeper into Conditional Access Policies, let’s consider the current cybersecurity landscape.
- Remote work has expanded the attack surface for many organisations
- Phishing attacks are becoming increasingly sophisticated
- Ransomware incidents are on the rise, with potentially devastating consequences
- Data breaches can result in significant financial and reputational damage
In this environment, a static, one-size-fits-all approach to security is no longer adequate. Organisations need dynamic, context-aware security measures that can adapt to different situations and threat levels.
5 Ways Conditional Access Policies Enhance Your Security
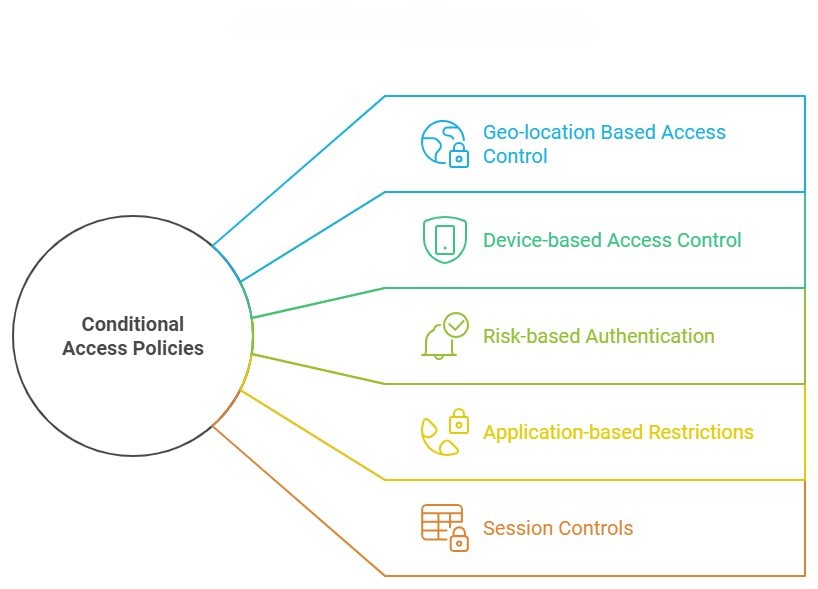
Let’s explore five keyways that Conditional Access Policies can dramatically improve your cybersecurity posture:
1. Geo-location Based Access Control
One of the most powerful features of Conditional Access Policies is the ability to restrict access based on geographic location.
How it works: You can set policies that only allow access from specific countries or regions where your business operates. Attempts to access your resources from other locations can be blocked or require additional verification.
Real-world example:
- The Problem: An Australian based Veterinarian practice was receiving consistent login attempts to Microsoft 365 accounts from multiple locations around the world, causing concerns for an account breach.
- The Solution: Conditional Access policies were implemented to restrict user access to countries the Veterinarian practice traded from and dedicated IP restrictions of selected accounts that only needed to be accessed from the practices.
- The Result: Significant decrease in malicious user login attempts from blocked countries, and no accounts breaches for accounts only accessible from the practices.
2. Device-based Access Control
Ensuring that only trusted devices can access your resources is another crucial aspect of cybersecurity.
How it works: Conditional Access Policies can be set to only allow access from devices that are managed by your organisation or that meet certain security requirements.
Why it matters: This prevents scenarios where an employee might access sensitive company data from a personal device that lacks proper security measures. It also mitigates risks associated with lost or stolen devices. This is particularly important in the context of your organisation’s BYOD policy.
3. Risk-based Authentication
Microsoft’s cloud intelligence can detect signs of suspicious activity, which Conditional Access Policies can use to adjust authentication requirements in real-time.
How it works: If a login attempt is flagged as high-risk (e.g., it’s from an unfamiliar location or shows signs of bot activity), the policy can require additional verification steps or block access entirely.
Why it’s powerful: This adaptive approach means that routine, low-risk activities aren’t disrupted, but potential threats are met with appropriate security measures.
Real-world example:
- The Problem: A Mining organisation had an incident that almost allowed a fraudulent financial transaction to be processed.
- The Solution: Several Conditional Access policies were implemented, including Risk based access control, which uses Microsoft 365 intelligence to review user login and determine if there is any risk associated with the login and the level of risk for the login.
- The Result: All key financial and admin users are now assessed for each login, with Microsoft 365 determining any risk associated with the login session. Several key finance staff who were working via VPN were blocked when their sessions were re-authenticated after the VPN was disconnected, resulting in high-risk behaviour being detected, their accounts being blocked, and a password change required on login to unlock the account.
4. Application-based Restrictions
Not all company resources are equally sensitive. Conditional Access Policies allow you to set different access requirements for different applications or data types.
How it works: You might set a policy that allows broad access to the company intranet but requires multi-factor authentication and a company-managed device to access financial systems.
Real-world example:
- The Problem: An education institute required user access to email, Teams and SharePoint to be limited to only Microsoft applications on personal devices, allowing for greater control of the data.
- The Solution: Conditional Access policies that specifically target any access form a personal device and restricting access on this device to Microsoft Apps only.
- The Result: All users accessing the education Institute data for a personal device were required to install the Microsoft Company Portal App to allow management of institute data on their devices and enforce all policies applied to personal devices. This resulted in the institute finding multiple mobile devices that did not have any unlock code and multiple users who were accessing data from non-Microsoft apps that were not manageable via MDM.
5. Session Controls
Conditional Access doesn’t stop working after the initial authentication. It can also control what users can do during their sessions.
How it works: Policies can be set to limit activities like downloading, printing, or copying data from certain applications, even after a user has been granted access.
Why it matters: This can prevent data exfiltration attempts, where a bad actor who has gained access tries to download large amounts of sensitive data.
Real-world example:
- The Problem: An educational institute required that user access to email, Teams chat, and SharePoint documents could not be saved on personal devices.
- The Solution: Conditional Access policies that specifically target any access form a personal device, implementing session controls to block saving on these devices.
- The Result: Users accessing institute data on personal devices was blocked from saving emails, Teams chat and SharePoint documents, users were required to download and install the Microsoft Company Portal app and verify their account. allowing session controls on personal devices and blocking saving data outside of approved Microsoft apps.
Case Study: How our Client Improved Their Security with Conditional Access
Let’s look at how one of our clients, a mid-sized financial services firm, leveraged Conditional Access Policies to enhance their security:
Before implementing these policies, Company X had experienced several minor security incidents, including a case where an employee’s credentials were used to access company data from overseas during a time when the employee wasn’t traveling.
We helped them implement a comprehensive set of Conditional Access Policies, including:
- Geo-location restrictions
- Device management requirements
- Risk-based authentication
The result? In the six months following implementation:
- Suspicious access attempts decreased by 90%
- There were zero successful unauthorised access incidents
- Employee reports of account lockouts due to forgotten passwords decreased, thanks to the more nuanced, risk-based approach
While the IT team initially worried about user pushback, they found that most employees appreciated the additional security, especially once they understood how it protected both the company and their own personal information.
Conclusion
In an era where cyber threats are constantly evolving, static security measures are no longer enough. Conditional Access Policies provide a dynamic, intelligent approach to cybersecurity that can dramatically improve your organisation’s security posture.
By implementing these policies, you can:
- Reduce your risk of data breaches
- Gain greater control over how and where your company resources are accessed
- Adapt your security measures in real-time to respond to potential threats
- Improve overall compliance with data protection regulations
Remember, cybersecurity is not a one-time effort, but an ongoing process. Regularly reviewing and updating your Conditional Access Policies should be a key part of your overall security strategy.
How Grassroots IT Can Help
At Grassroots IT, we specialise in helping businesses leverage the full power of Microsoft 365, including advanced security features like Conditional Access Policies. Our team of experts can:
- Assess your current security posture
- Design and implement Conditional Access Policies tailored to your specific needs
- Provide ongoing support and optimisation of your policies
- Train your team on best practices for cybersecurity
Don’t wait for a security incident to occur. Take proactive steps to protect your organisation today. Contact us for a consultation, and let’s explore how we can enhance your cybersecurity with Conditional Access Policies.
Data protection isn’t just a nice-to-have—it’s a critical business imperative. Australian businesses face an increasingly complex web of regulations designed to safeguard personal information. But here’s the good news: if you’re using Microsoft 365, you’ve already got a powerful ally in your corner.
Let’s dive into how Microsoft 365 can help you navigate the choppy waters of data protection regulations in Australia, and how you can leverage its features to not just comply but thrive.
Understanding Australian Data Protection Regulations
Before we jump into the tech, let’s recap the regulatory landscape:
- The Privacy Act 1988 and its 13 Australian Privacy Principles (APPs) form the backbone of data protection law in Australia. These principles cover everything from the collection and use of personal information to its disclosure and security.
- The Notifiable Data Breaches (NDB) scheme requires organisations to notify affected individuals and the Office of the Australian Information Commissioner (OAIC) when a data breach is likely to result in serious harm. This means you need to have robust systems in place to detect, assess, and respond to data breaches quickly.
- Various industries have additional requirements, like APRA CPS 234 for financial services, which mandates specific information security practices.
Sounds daunting, right? Don’t worry—Microsoft 365 has got your back. Let’s explore how.
Microsoft 365 Compliance Center: Your Central Hub
Think of the Microsoft 365 Compliance Center as your control room for all things compliance. It gives you a bird’s-eye view of your compliance posture across your Microsoft 365 environment.
The Compliance Manager feature helps you track your progress towards meeting regulatory requirements. It provides a set of controls and improvement actions based on common regulations and standards. For each improvement action, you get step-by-step implementation guidance, which is incredibly helpful when you’re trying to navigate complex compliance requirements.
The Compliance Score, on the other hand, gives you a quantitative measure of your compliance efforts. It’s calculated based on the controls you’ve implemented and their relative importance. This score can be a great way to demonstrate your compliance efforts to stakeholders and identify areas for improvement.
Data Classification and Protection
One of the key requirements of APP 11 is ensuring the security of personal information. Microsoft 365’s sensitivity labels and Azure Information Protection allow you to classify and protect data based on its sensitivity.
Here’s how it works: You can create labels like “Confidential” or “Strictly Confidential” and define what happens when these labels are applied to documents or emails. For example, a “Strictly Confidential” label might automatically encrypt the document and restrict forwarding.
You can even use machine learning to automatically detect and label sensitive information like credit card numbers or health records. This means you can automatically apply protection actions like encryption or access restrictions to sensitive data, reducing the risk of unauthorised access.
Data Loss Prevention (DLP) Policies
Ever worried about sensitive information being shared accidentally? Microsoft 365’s DLP policies have got you covered. You can set up policies to prevent unauthorised sharing of sensitive information, aligning neatly with APP 6’s requirements around the use and disclosure of personal information.
For instance, you could create a policy that detects when a document contains multiple credit card numbers and blocks it from being shared outside your organisation. Or you could set up a policy that warns users when they’re about to send an email containing what looks like a tax file number.
These policies work across Microsoft 365, including in email, SharePoint, OneDrive, and Teams, providing comprehensive protection.
Retention and Deletion Policies
APP 11.2 requires the destruction or de-identification of personal information when it’s no longer needed. Microsoft 365’s retention and deletion policies allow you to automate this process, ensuring that data is retained only as long as necessary and then securely deleted.
You can create policies based on a variety of conditions. For example, you might set a policy to retain all emails for 7 years and then automatically delete them. Or you could create a policy that retains documents in a specific SharePoint site for 3 years after they were last modified.
These policies help ensure you’re not keeping data longer than necessary, which not only helps with compliance but can also reduce storage costs and minimise risk.
Auditing and Reporting
Many of the APPs require you to keep records of how personal information is handled. Microsoft 365’s comprehensive auditing capabilities and customisable reports make it easy to demonstrate compliance when needed.
The unified audit log records user and admin activities across many Microsoft 365 services. You can search this log to investigate potential security or compliance issues, or to respond to legal or regulatory requests.
You can also create custom reports to track specific activities or compliance metrics. These reports can be invaluable when you need to demonstrate your compliance efforts to auditors or regulators.
Secure Access and Identity Management
Azure Active Directory, part of the Microsoft 365 suite, provides robust identity and access management capabilities. Implementing features like multi-factor authentication can significantly enhance your data security, helping you meet the requirements of APP 11.
But it goes beyond just multi-factor authentication. Azure AD also offers features like:
- Conditional Access, which allows you to create policies that either allow or block access based on factors like user location, device status, and real-time risk detection.
- Privileged Identity Management, which helps you minimise the number of people who have access to secure information or resources, reducing the risk of malicious actions.
- Access Reviews, which allow you to regularly review and recertify user access, ensuring that users only have the access they need.
Responding to Data Breaches
The NDB scheme requires prompt notification of serious data breaches. Microsoft 365’s advanced threat protection features, including Insider Risk Management and Communication Compliance, can help you detect potential breaches early.
Insider Risk Management uses machine learning to identify potential insider risks, like data leaks or intellectual property theft. It analyses signals across Microsoft 365, spotting patterns that might indicate a problem.
Communication Compliance helps you detect, capture, and take remediation actions for inappropriate messages. For example, it can detect offensive language, sensitive information sharing, or conflicts of interest in communications.
These tools give you a head start in responding and notifying affected parties if necessary, helping you meet the tight timeframes required by the NDB scheme.
Wrapping Up
Microsoft 365 offers a comprehensive set of tools to help you meet Australian data protection regulations. But remember, these tools are only effective when properly configured and managed. It’s like having a high-performance car—it’s great, but you need to know how to drive it to get the most out of it.
That’s where we come in. At Grassroots IT, we’ve been helping businesses navigate the complexities of IT and compliance for almost two decades. We’re not just here to set up your tech—we’re here to help you use it strategically to drive your business forward.
Want to know how well your current setup measures up? We offer a comprehensive Business Technology Review that can help you identify gaps in your compliance posture and opportunities for improvement. Get in touch with us today, and let’s make sure your business isn’t just compliant, but thriving.
Remember, in the world of data protection, an ounce of prevention is worth a pound of cure. Don’t wait for a breach to start taking compliance seriously—your business (and your customers) will thank you for it. With the right tools and expertise, you can turn compliance from a burden into a competitive advantage. Let’s make it happen together.
Remote work has become more than just a trend – it’s now a fundamental part of how many Australian businesses operate. While this shift brings numerous benefits, it also presents new challenges in data security. With team members accessing sensitive information from various locations and devices, how can you ensure your data remains protected? This is where Data Loss Prevention (DLP) becomes crucial.
The Remote Work Security Challenge
Remote work has expanded the traditional network perimeter, making it more difficult to control and monitor data access and movement. Your team members might be working from home in Brisbane, from a client’s office in Sydney or a cafe in Melbourne. They’re likely using a mix of company-issued and personal devices, connecting through various networks of varying security levels.
In this distributed environment, the risks of data leaks – both accidental and intentional – increase significantly. An employee might inadvertently send sensitive information to their personal email for easier access or to save confidential documents to an unsecured cloud storage service. Without proper safeguards, your valuable business data could be exposed to unauthorised access or breaches.
Enter Data Loss Prevention (DLP)
DLP is a set of tools and strategies designed to detect potential data breaches and prevent them by monitoring, detecting, and blocking sensitive data while in use, in motion, and at rest. In a remote work context, DLP becomes your virtual security guard, ensuring that your data is protected regardless of where your team members are located.
Key DLP Strategies for Remote Work
- Content Awareness: Modern DLP solutions can identify sensitive information based on predefined patterns, keywords, or file properties. This means you can set up policies to protect specific types of data, such as financial records or client information, regardless of where it’s stored or how it’s being accessed.
- Context-Based Policies: DLP isn’t just about blocking all data movement. It’s about understanding the context of data use. For example, you might impose restrictions on documents labelled as “Top Secret,” block emails sent to specific domains, or prevent sharing files with certain extensions. You can also tailor access controls based on the sensitivity of the data and the specific circumstances of its use.
- User Education and Alerts: One of the most powerful features of DLP is its ability to educate users in real-time. When an employee is about to violate a policy, the DLP system can alert them, explaining why the action is risky and suggesting secure alternatives.
- Endpoint Protection: With remote work, every device becomes an endpoint that needs protection. DLP can be extended to laptops, tablets, and even smartphones, ensuring that data is protected even on personal devices used for work.
- Cloud Application Control: As remote teams rely heavily on cloud applications, DLP can monitor and control data sharing across these platforms, preventing unauthorised sharing or downloads.
Implementing DLP for Remote Work: A Hypothetical Case Study
Let’s consider a mid-sized engineering firm based in Brisbane. With their team of 50 now working remotely, they implemented a DLP solution to secure their client data and creative assets. Here’s how they approached it:
- They started by categorising their data, identifying what was most sensitive (e.g., client strategies, financial information) and what was less critical.
- They set up DLP policies to monitor emails and file transfers, alerting employees if they attempted to send sensitive information to personal email addresses or unauthorised third parties.
- For their design team working with large files, they implemented policies that allowed the use of approved cloud storage solutions but blocked uploads to personal accounts.
- They used endpoint DLP on all company-issued laptops, ensuring that sensitive data couldn’t be copied to USB drives or other external storage without approval.
- The DLP system was configured to provide real-time education to employees, explaining why certain actions were blocked and suggesting secure alternatives.
The (hypothetical) result? In the first month alone, the agency prevented several potential data leaks, including an instance where a new employee almost sent a confidential client brief to their personal email. The system not only blocked the transfer but also educated the employee about the proper protocols for handling sensitive information.
Best Practices for DLP in Remote Work Environments
- Start with Clear Policies: Before implementing technical solutions, ensure you have clear, written policies about data handling in remote work situations. Make sure all employees understand these policies.
- Use a Graduated Approach: Start with monitoring and alerting before moving to more restrictive blocking policies. This allows you to understand your data flow and refine your approach.
- Focus on User Experience: The goal is to protect data without hindering productivity. Choose DLP solutions that offer seamless user experiences and integrate well with your existing tools.
- Regular Training: Complement your DLP implementation with regular security awareness training. The more your team understands about data security, the more effective your DLP strategy will be.
- Continuous Monitoring and Adjustment: The remote work landscape and potential threats are continually evolving. Regularly review and adjust your DLP policies to ensure they remain effective.
Conclusion
As remote work continues to be a significant part of our business landscape, protecting your data has never been more crucial. DLP provides a powerful set of tools to secure your sensitive information, regardless of where your team members are working from. By implementing a well-thought-out DLP strategy, you can enjoy the benefits of remote work while maintaining the security of your valuable business data.
The digital landscape has seen a fundamental shift in how businesses operate, with remote work becoming more than just a trend. While this flexibility brings numerous benefits, it also introduces new challenges in securing business data and maintaining a robust cybersecurity posture.
As your team members access sensitive information from various locations and devices, how can you ensure that your business data remains protected? Enter Microsoft Entra ID (formerly Azure AD) and Intune—two powerful tools that, when combined, provide a comprehensive solution for securing your remote workforce.
Understanding the Security Challenges of Remote Work
Before we dive into the solutions, let’s take a moment to understand the unique security challenges that come with remote work:
- Increased attack surface: With devices operating outside the corporate network, not only are traditional security controls such as corporate firewalls rendered powerless, but there are also more potential entry points for cybercriminals. This can include unsecured Wi-Fi networks, personal devices, and even the use of public computers.
- Data leakage risks: The use of personal devices for work purposes can lead to inadvertent data exposure. For example, a team member may unintentionally save sensitive company data on their personal cloud storage or accidentally share confidential information with unauthorised individuals.
- Policy enforcement difficulties: Maintaining consistent security policies across a distributed workforce can be challenging. Traditional methods of enforcing policy, such as Active Directory, are unreliable at best with a remote workforce. This can lead to inconsistent security practices and increased vulnerability.
- Shadow IT: Remote workers might resort to using unauthorised applications or services to get their work done, potentially exposing company data to unsecured platforms. This “shadow IT” can be difficult to detect and control in a remote environment.
Microsoft Entra ID: The Foundation of Identity Security
At the heart of securing your remote workforce is robust identity management. This is where Microsoft Entra ID shines.
Entra ID is a cloud-based identity and access management service that forms the backbone of security for Microsoft 365 and many other cloud applications. For securing and protecting remote workers, Entra ID offers several key benefits:
- Single Sign-On (SSO): Allows users to access multiple applications with one set of credentials, improving both security and user experience. This reduces the likelihood of employees using weak or repeated passwords across multiple services.
- Multi-Factor Authentication (MFA): Adds an extra layer of security by requiring two or more verification methods to access resources. This significantly reduces the risk of unauthorised access, even if passwords are compromised.
- Conditional Access: Enables you to control access to your apps and data based on identity, device, and risk signals. For example, you can require additional authentication steps for access from unfamiliar locations or devices.
By implementing Entra ID, you create a strong foundation for securing your remote workforce’s identities and controlling access to your business resources. And the good news is, if you already have a Microsoft 365 subscription, you already have access to Entra ID.
Intune: Comprehensive Device Management for Remote Workers
While Entra ID secures identities, Microsoft Intune takes care of device and application management. Intune is a cloud-based service that focuses on mobile device management (MDM) and mobile application management (MAM).
Key features of Intune include:
- Device enrolment: Easily enrol and manage devices across various platforms (Windows, iOS, Android). This allows you to maintain control over both company-owned and personal devices used for work, even allowing you to remote-wipe a device in the event it becomes lost.
- Application management: Deploy and manage apps on remote devices, ensuring your team has the tools they need. This includes the ability to push required apps to devices and remove them when necessary.
- Device compliance: Set rules, assess device compliance and deploy policies to protect company data. For instance, you can require devices to have up-to-date antivirus software and encrypted storage.
With Intune, you can ensure that all devices accessing your business data—whether company-owned or personal—meet your security standards.
Combining Entra ID and Intune for Robust Security
The real magic happens when you combine the powers of Entra ID and Intune. Together, they provide a comprehensive security solution for your remote workforce:
- Conditional Access policies: Use Entra ID’s Conditional Access in conjunction with Intune’s device compliance to control resource access based on user, device, and risk factors. For example, you can require that devices be managed by Intune and compliant with your policies before allowing access to company resources.
- App protection policies: Protect your data at the application level, preventing unauthorised sharing or saving of company information. This is particularly useful for BYOD scenarios where you need to separate personal and work data on the same device.
- Automated enforcement: Ensure compliance requirements are met on remote devices without manual intervention. Non-compliant devices can be automatically blocked from accessing company resources until they meet the required standards.
Conclusion
Securing your remote workforce doesn’t have to be a headache. With Microsoft Entra ID and Intune, you have a powerful combination of tools at your disposal to protect your business data, manage devices, and ensure compliance—all while providing a seamless experience for your remote team.
By implementing these solutions, you’re not just reacting to the challenges of remote work; you’re proactively building a secure, flexible, and productive work environment for the future. You’re empowering your team to work from anywhere, without compromising on security.
Ready to take the next step in securing your remote workforce? At Grassroots IT, we’ve been helping businesses like yours navigate the complexities of IT security for almost 20 years. Get in touch today for a free consultation and let’s explore how we can empower your remote team while keeping your data safe.
With new and evolving cybersecurity threats emerging almost daily, the risk to businesses is greater than ever. A 2023 study by IBM reports that the average cost of a data breach in Australia is now $4.3 million. While this figure is less than the global average of $4.45 million, the escalation of cybersecurity threats shows no sign of slowing anytime soon.
So, the critical question is, how do you keep your organisation safe in such a hostile cyber environment? The best place to start is by educating yourself on the nature of cybersecurity risks and the options available to help mitigate them.
In this post, we discuss the top five cybersecurity threats to be aware of in 2024. These are the most common threats that we see in our work helping clients mitigate these risks and respond to incidents.
1. Increased Impact from Malicious AI Tools
Artificial Intelligence (AI) poses a significant threat, not just as a tool for innovation but also as a potential weapon in the hands of cybercriminals.
AI can be exploited by cybercriminals to conduct more sophisticated attacks with increased precision and frequency. These AI-driven attacks can bypass traditional cybersecurity measures, making detection and defence more challenging for organisations.
Strategies to Combat Malicious AI Tools:
Developing strategies to counteract malevolent AI tools is important for safeguarding your organisation against complex threats. By remaining proactive and employing security practices, you can diminish the risks and consequences of AI-powered cyber-attacks. Here are helpful strategies to combat these threats:
- Continuous Monitoring: Implement AI-driven security tools that monitor network activity to detect and respond to anomalies. These tools can detect anomalies and respond promptly to any suspicious behaviour.
- Advanced Threat Intelligence: Leverage platforms that use AI to predict and identify potential threats before they can cause harm.
- Regular Security Audits: Conduct frequent cybersecurity risk assessments to identify vulnerabilities and ensure all security protocols are up to date.
Organisations can enhance their protection against the increasing threat of malicious AI by staying proactive and utilising AI defence tools.
2. Phishing
Phishing is one of the most common forms of attack whereby fake emails are sent purporting to be from sources familiar to the target, such as the Commonwealth Bank, Australia Post or Microsoft. The goal of phishing is to trick individuals into granting access to secure systems by either handing over password details or allowing the installation of malware onto their computer. Once the attacker has gained access to company systems, they may explore and plan their next steps undetected.
Protecting Against Phishing
- Multi-factor Authentication (MFA): Even if an attacker obtains password details, MFA adds a layer of security. Most modern applications support MFA, though it may not be enabled by default.
- Email Filtering: Effective email filtering can stop many phishing emails before they reach employee inboxes. Advanced filtering is available for major platforms like Microsoft Office 365.
- User Education: Employee awareness is critical. Educating your workforce on recognising and avoiding phishing attacks is an effective risk mitigation strategy.
3. Business Email Compromise
Business email compromise is a strategy used by attackers to defraud a target company, employed once they have gained access to secure systems via other means. With access to company systems, they will gather information regarding financial processes, payment systems and client relationships. They will monitor email communications to learn who in the organisation has financial authority and the language and methods that they use to communicate.
Once they have the information that they need, attackers will then seek to deceive employees, clients and business partners into making payments to their bank accounts rather than genuine ones. These fraudulent requests for funds can be difficult to identify and lost funds can be challenging to trace and recover. The potential for direct financial loss through business email compromise is significant.
Protecting Against Business Email Compromise
- Multi-factor Authentication (MFA): MFA effectively defends against many user account attacks.
- User Education: Employees involved in financial transactions must be vigilant and take all necessary precautions.
- Verification Processes: Implement secondary verification (e.g., phone calls) for all financial transactions and change of detail requests.
4. Social Engineering
Cybercriminals will often seek to gain the trust of their targets in order to elicit the information that they need to breach secure systems. Any form of social interaction with the malicious intent of gaining access to secure systems can be considered social engineering. A common approach is to create fictitious personas on social media which are then used to establish fake relationships with potential victims and trick them into allowing access to company systems.
Protecting Against Social Engineering
- User Education: Training employees to identify and respond to social engineering threats is essential.
- Endpoint Protection: Use advanced endpoint protection software to detect and block malicious software.
- Multi-factor Authentication (MFA): MFA provides robust defence against user account breaches, even if passwords are compromised.
5. Ransomware
Ransomware is a particular form of malicious software (aka malware) that, once active within a computer system, will encrypt critical data rendering it inaccessible until a ransom is paid. Unfortunately for some business owners, even when a ransom is paid, access to the data is not always restored. Ransomware is responsible for some of the largest and highest profile security incidents in recent times. A ransomware attack can be devastating to any organisation, grinding operations to a halt.
Protecting against Ransomware
All forms of malware including ransomware can be mitigated with strategies such as:
- Endpoint protection: All computer systems must be protected with advanced endpoint protection software.
- System updates: Computer systems without up-to-date software and operating systems are a common weakness that attackers can exploit.
- Isolated backups: Not only should backups be monitoring and tested regularly, but a copy should be stored separately and unattached to the main systems to protect attackers from being able to compromise backups.
- User education: Human error is common factor in many malware infections. Training employees to recognise a potential malware infection and respond accordingly is critical.
6. Supply Chain Attack
A supply chain attack is a form of cyber-attack where malicious actors target an organisation indirectly through less secure partners in their supply chain, most commonly software vendors. The attackers aim to compromise a particular software application which, once deployed in the target organisation’s network, allows unauthorised access to company systems. Such attacks can have widespread repercussions, as compromising one link in the supply chain can potentially grant access to multiple interconnected organisations.
Although not strictly a supply chain attack, it’s important to highlight the necessity for supply chain cyber-resilience. An attack on your supply chain can be just as disruptive as an attack through your supply chain. Disruptions to key suppliers can cause significant operational downtime and extend vulnerabilities within your organisation.
Protecting against Supply Chain Attack
- Risk management: Include Supply Chain in risk management plans, including disaster recovery and cybersecurity incidents.
- Least trust security: Limit supplier access to the minimum required.
- Vendor security requirements: Incorporate clear vendor security requirements into supply agreements.
Watch our free on-demand webinar now: Managing the Risk of Supply Chain Attack.
Conclusion
Cybersecurity starts with an understanding of the threats that your organisation may face, and the options available to you to mitigate those risks. From there you can prioritise and focus your cybersecurity efforts with confidence.
For help protecting your business, speak with one of our cybersecurity experts today.
