The Real Cost of Cybersecurity Decision Paralysis
The most expensive cybersecurity decision most Brisbane businesses make isn’t the wrong product or the wrong vendor. It’s the decision to keep putting off a decision.
We see this pattern regularly: a business leader knows the security posture needs attention. They’ve probably known for a year or more. So they request a couple of quotes, attend a webinar, bookmark a few articles, and tell themselves they’re being diligent. Meanwhile, the calendar moves forward and the actual risk doesn’t go anywhere.
What looks like prudent deliberation is often something else: decision paralysis. And unlike a bad vendor choice, which you can reverse, paralysis has a way of quietly running up a bill that never appears on an invoice.
Why Smart People Delay Cybersecurity Decisions
Decision paralysis around cybersecurity isn’t irrational. It comes from concerns that are genuinely legitimate.
- Option overwhelm. Every vendor claims their solution is the critical one – firewalls, endpoint protection, security awareness training, vulnerability scanning, penetration testing. Without a trusted framework for prioritising, everything feels equally urgent, which is functionally the same as nothing feeling actionable.
- Budget uncertainty. Quotes range wildly. One consultant quotes $8,000 for an assessment. Another quotes $45,000 for implementation. A third suggests a $120,000 full-time hire. Without context for what your business actually needs, there’s no rational basis for choosing between them.
- Fear of making the wrong call. What if the technology changes? What if the implementation creates a false sense of security? These are reasonable questions, and the stakes do feel high.
- Competing priorities. Cybersecurity sits alongside product development, sales initiatives, and growth investments. It’s easy to tell yourself: we haven’t been breached yet, let’s focus on revenue-generating work first.
All of these concerns are valid. The problem is that whilst you’re carefully weighing them, costs are accumulating in ways that don’t show up until it’s too late to avoid them.
The Hidden Costs of Delayed Decisions
Decision paralysis carries real costs – most of which don’t appear on invoices or in budgets. Here’s what accumulates whilst you delay:
Cost 1: Rising Insurance Premiums
Cyber insurance premiums have increased 50-100% over the past three years. Insurers now require detailed security questionnaires. Without demonstrated maturity – certifications, documented controls, evidence of ongoing management—you’re in the high-risk category.
The cost: For a typical Brisbane SME, the difference between high-risk and demonstrated-maturity premiums can be $5,000-15,000 annually. That’s $60,000-180,000 over three years of delayed security improvements.
Cost 2: Lost Tender Opportunities
More RFPs require security certifications or demonstrated framework compliance. If you can’t tick those boxes, you’re not even shortlisted. Your competitors with Essential Eight or ISO 27001 certifications win by default.
The cost: How many tenders have you declined or not pursued because you knew you couldn’t meet security requirements? Even one missed $100,000+ contract dwarfs most security investments.
Cost 3: Client Confidence Erosion
When clients send security questionnaires and you can’t answer confidently, you’re creating doubt. “We’re working on it” or “That’s on our roadmap” sounds like you’re not taking their data seriously.
The cost: Client relationships are hard to quantify, but erosion is real. Clients who lose confidence in your security posture start evaluating alternatives. By the time they switch, it’s too late to rebuild trust.
Cost 4: Leadership Time Waste
How many hours have you and your leadership team spent researching cybersecurity, getting quotes, attending vendor demonstrations, reviewing proposals, and discussing options without reaching decisions?
The cost: If your leadership team has spent 10 hours monthly for six months researching without deciding, that’s 60 hours. At $200/hour opportunity cost, that’s $12,000 spent on indecision – with nothing to show for it.
Cost 5: Catching Up Is More Expensive
When you finally must improve security – because an insurer demands it, a client requires it, or a regulation mandates it – you’re implementing under pressure. Rushed implementations cost more:
- Premium rates for urgent work
- Mistakes from rushed deployment
- Business disruption from quick changes
- Lack of proper evidence collection
The cost: Urgent security projects typically cost 30-50% more than planned implementations. Plus, quality suffers when you’re racing deadlines.
Cost 6: Regulatory Exposure
Privacy and security regulations are tightening globally. The Australian Privacy Act amendments, mandatory breach notification requirements, and industry-specific regulations all increase compliance obligations.
Businesses that haven’t built security maturity face regulatory risk. When breaches occur – and statistically, they will – demonstrable security efforts influence both regulatory response and public perception.
The cost: Regulatory fines, legal fees, remediation costs, and reputational damage. For Australian businesses, data breach costs on average $4.26 million according to IBM’s 2024 Cost of a Data Breach Report.
The Opportunity Cost of Inaction
Beyond direct costs, decision paralysis carries opportunity costs—benefits you forgo by not improving security:
Competitive Advantage Lost
Security maturity is becoming a competitive differentiator. Businesses that can demonstrate Essential Eight compliance or ISO 27001 certification win contracts against competitors who can’t. They command premium pricing because clients value demonstrated security.
Whilst you delay, competitors are building this advantage.
Strategic Clarity Missed
Businesses with strong security posture make better strategic decisions. They can confidently pursue cloud migrations, enable remote work, adopt new technologies, and expand into regulated industries—all opportunities that require security confidence.
Decision paralysis on security creates decision paralysis on strategy.
Peace of Mind Deferred
There’s a psychological cost to ongoing uncertainty. Business leaders who aren’t confident in their security spend mental energy worrying. Every news story about a breach triggers anxiety. Every client questionnaire creates stress.
Confidence in your security posture frees mental bandwidth for growth activities.
What Breaks the Paralysis
Understanding the costs of inaction helps, but it doesn’t answer the underlying question: where do you actually start?
In our experience, what breaks the cycle isn’t more information – it’s structure. Most of the businesses we work with that have been stuck in research mode for months aren’t lacking data; they’re lacking a decision-making framework and someone they trust to guide them through it.
Trusted guidance matters more than most people realise. When you’re evaluating vendors who all have an interest in the outcome, you can’t get unbiased prioritisation. What actually moves things forward is an adviser who can look at your specific situation and say: given where you are, here’s what matters first, and here’s what can wait.
Recognised frameworks like Essential Eight and SMB1001 are genuinely useful here — not because they make the decision for you, but because they dramatically reduce the number of decisions you need to make. Instead of evaluating every possible security improvement against every other, you’re working through a structured set of proven controls that insurers, clients, and regulators already recognise. The scope becomes manageable.
Staged investment helps too. You don’t need to commit to everything at once, and framing security improvement as a 12-month journey rather than a single project changes the calculus entirely.
But the thing that matters most – and what we see makes the biggest difference – is simply a clear starting point. Most businesses delay because they don’t know where they currently stand. A baseline assessment against a recognised framework gives you that. Once you know the gap between where you are and where you need to be, the next decision becomes obvious rather than overwhelming.
The Cost-Benefit Reality
Let’s put the costs of inaction into perspective with actual numbers:

Meanwhile, strategic cybersecurity investment typically ranges from $30,000-60,000 annually for comprehensive guidance and implementation.
The question isn’t whether you can afford to invest in cybersecurity. It’s whether you can afford to keep delaying.
Breaking Free From Paralysis
If you recognise your business in any of this, the path forward is simpler than the research phase has probably made it feel.
The gap between where most businesses are and where they need to be is almost always smaller than the paralysis suggests. And the businesses that finally move forward consistently say the same thing: the relief of having a concrete plan, rather than an open-ended research project, was immediate. The hard part wasn’t the work. It was making the first move.
Start by acknowledging that inaction has a cost. Then get a baseline. From there, the decisions get progressively easier, because you’re working from facts rather than estimates.
If you’d like to understand where you currently stand, a baseline assessment against Essential Eight or SMB1001 is the natural first step.
The Bottom Line
The businesses that make real security progress aren’t necessarily the ones with the biggest budgets. They’re the ones who’ve recognised that structured action, even imperfect action, beats indefinite research.
If you’ve been stuck in cybersecurity decision paralysis, calculate what delay is actually costing you. The number might surprise you, and it might be exactly what finally moves things forward.
Ready to move from research to action? The first step is understanding where you currently stand. A baseline security assessment can break decision paralysis by giving you concrete starting point. Contact us today to discuss your current cybersecurity posture and next best steps forward.
Why Knowing Cybersecurity Is Important Isn't Enough
Every business leader knows cybersecurity matters. Yet most still struggle to make meaningful progress. The problem isn’t awareness – it’s knowing what to do next.
Most Brisbane business leaders we speak to can articulate the cybersecurity risks their business faces. They’ve read the breach headlines. They know their clients are asking harder questions. They understand the insurance market has changed.
Awareness is no longer the problem.
What most businesses haven’t solved is what comes after awareness: making confident, informed decisions about what to actually do. Ask a business leader what specifically they’re working on, how they decided those were the right priorities, and how they measure progress and that’s usually where the certainty evaporates.
The Awareness Plateau
Over the past decade, cybersecurity awareness has skyrocketed. Businesses understand the risks. They’ve read the headlines about ransomware attacks. They know client data needs protecting. They’re aware insurance companies are asking harder questions.
Awareness is no longer the problem.
The problem is what comes after awareness: making informed decisions about what to actually do.
Most businesses get stuck on what we call the Awareness Plateau. They know cybersecurity matters, but without expertise to guide decisions, they’re left guessing:
- Should we invest in a new firewall or focus on user training first?
- Is multi-factor authentication more urgent than application control?
- Should we commission another security audit or actually implement the last one?
- How do we know if we’re making real progress or just ticking boxes?
These aren’t questions about whether cybersecurity matters. They’re questions about how to make progress when you don’t have internal expertise to guide the journey.

The Decision Dilemma
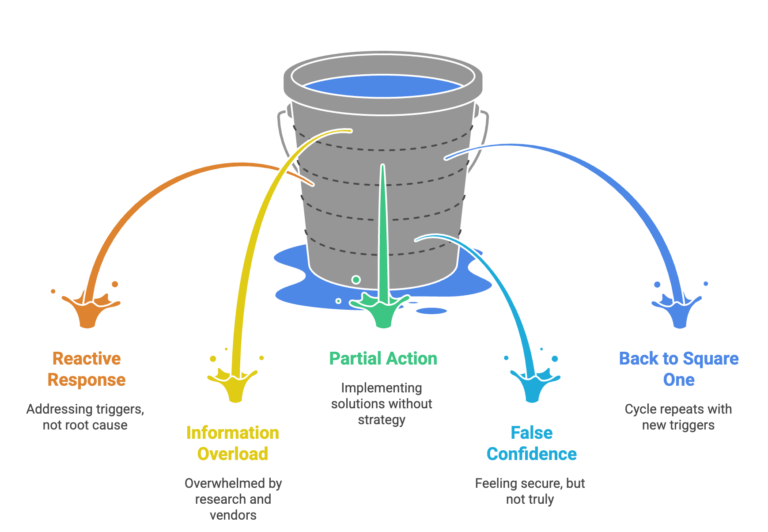
Here’s what the decision-making process looks like for most businesses without dedicated cybersecurity expertise, and it tends to follow a familiar pattern.
Something triggers concern: a client questionnaire, an insurance renewal, a news story about a breach that hits close to home. So the research begins. Google returns millions of results, every vendor claims their solution is the critical one, and the more you read, the more overwhelming it becomes.
Eventually, something gets implemented, usually whatever seemed most urgent or was recommended by the last person you spoke to. A firewall upgrade, a security audit, a new backup solution. For a while, it feels like progress. The immediate concern is addressed and security feels handled.
Then, six months later, another trigger arrives. A different client questionnaire. A new insurance requirement. And the realisation sets in: you’re still not confident about your overall security posture. You still don’t know if you’re focusing on the right things. You’re back to square one.
This cycle repeats because the underlying problem hasn’t changed: security decisions are being made without security expertise to guide them.
Why General IT Support Isn't Enough
Many businesses assume their IT support provider handles cybersecurity. And in a sense, they do – but there’s a critical distinction most people miss.
Your IT support keeps your environment secure operationally. They patch systems, configure firewalls, manage antivirus, respond to incidents, and maintain security configurations. This is essential – it’s your security foundation.
But operational security and strategic security are different capabilities:
Operational Security (What IT Support Provides):
- Keeping systems patched and updated
- Maintaining secure configurations
- Responding to security incidents
- Implementing technologies when requested
- Following best practices
Strategic Security (The Missing Layer):
- Assessing current maturity against recognised frameworks
- Prioritising improvements based on risk and business context
- Building systematic capability over time
- Collecting evidence for certifications and audits
- Demonstrating maturity to insurers, clients, and regulators
Think of it this way: operational security keeps your house locked and the alarm working. Strategic security ensures you’re protecting the right rooms, meeting building codes, and can prove it to your insurer.
You need both. But most businesses only have the operational layer.
The Framework Gap
When businesses do seek strategic guidance, they often turn to security frameworks like Essential Eight or ISO 27001. These frameworks are excellent – they represent best practice distilled from thousands of organisations’ experiences.
But here’s what many businesses discover: frameworks tell you what good security looks like. They don’t tell you how to get there from where you are now.
Essential Eight, for example, specifies eight critical controls. For each control, it defines three maturity levels. The documentation is comprehensive and freely available.
Yet businesses still struggle to implement it. Why?
- Prioritisation: Which control should you implement first? The answer depends on your current environment, industry, risk profile, and capacity. The framework doesn’t tell you.
- Implementation: The framework says ‘implement application control.’ But how? Which technology? What’s the rollout sequence? How do you handle exceptions? The framework doesn’t specify.
- Verification: You’ve implemented what you think is application control. But is it configured correctly? Will it pass audit? The framework doesn’t verify.
- Evidence: You need to prove compliance. What evidence do auditors expect? When do you collect it? The framework doesn’t guide evidence collection.
- Momentum: Implementation takes months. How do you maintain progress when business priorities shift? The framework doesn’t provide accountability.
Frameworks are maps. But maps don’t navigate for you. You still need a guide who knows the territory.
The One-Off Audit Trap
Recognising they need expert guidance, many businesses commission a security audit or assessment. This seems logical: get an expert to evaluate your security and recommend improvements.
And it works – to a point. You receive a comprehensive report identifying vulnerabilities and recommending controls. For a moment, you feel clarity. Finally, someone has told you what to do.
Then the report arrives. Forty-seven recommendations. Prioritised as ‘Critical,’ ‘High,’ ‘Medium,’ and ‘Low.’ All valid. All important. All overwhelming.
Now you face new questions:
- Should we tackle all the ‘Critical’ items first, even though some are expensive and complex?
- Or should we pick some ‘Quick wins’ to build momentum?
- Six months from now, will these priorities still be right?
- How do we know if we’re implementing them correctly?
- What evidence should we collect to prove we’ve addressed each recommendation?
The audit provided a snapshot. But you need ongoing navigation. Without continued guidance, most audit reports end up filed away, with scattered implementation attempts that never build into coherent security maturity.
One-off audits create what we call ‘Point-in-Time Clarity’—you understand your security posture on the day of the audit. But security is a journey, not a destination. The clarity fades as your environment changes, threats evolve, and you implement controls without verification.
What Strategic Cybersecurity Guidance Actually Looks Like
So if awareness isn’t enough, frameworks need interpretation, IT support handles operations not strategy, and one-off audits leave you stuck—what does work?
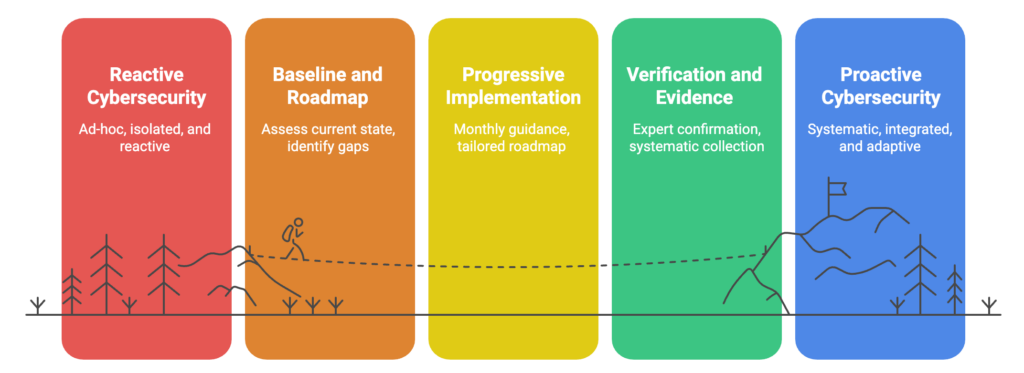
Strategic cybersecurity guidance provides what’s missing: ongoing expert advice that helps you make informed decisions month by month.
Here’s what that looks like in practice:
Month 1: Baseline and Roadmap
Assess where you are across recognised frameworks. Identify what you’ve already implemented and where gaps exist. Create a prioritised roadmap based on your specific situation—not generic recommendations, but tailored guidance considering your industry, risk profile, budget, and capacity.
Months 2-12: Progressive Implementation
Monthly meetings guide you through implementing the next controls on your roadmap. Not rushed—at a pace that suits your team’s capacity. Some months you tackle multiple improvements. Other months you focus on embedding one change properly whilst managing other business priorities.
When obstacles arise, you have expert guidance to overcome them. When circumstances change, the roadmap adapts. When new threats emerge, priorities adjust.
Throughout: Verification and Evidence
As you implement each control, expert verification confirms it’s done properly. Evidence is collected systematically—not scrambled together when audit time arrives. When you’re ready for certifications, everything is organised and prepared.
This approach transforms cybersecurity from guesswork into systematic capability building. You’re not wondering if you’re doing the right things—you have ongoing expert confirmation. You’re not stuck implementing an audit report in isolation—you have continuous guidance adapting to your reality.
Moving Beyond Awareness
The businesses that make real security progress aren’t necessarily the most aware of cybersecurity risks. They’re the ones who’ve stopped treating security as a research project and started treating it as a capability to be built, steadily, with expert guidance.
The good news is that the path from awareness to action is more straightforward than the overwhelm suggests. It starts with understanding where you actually stand — not a rough sense of it, but a proper baseline against a recognised framework. From there, the decisions get progressively clearer, because you’re working from facts rather than estimates.
If you’re stuck on the Awareness Plateau, knowing cybersecurity matters but uncertain about what to do next, a baseline assessment is the natural first step.