Essential 8 Specialists
ISO 27001 Certified
Brisbane - Based Team
Right-Sized Approach
The Challenge
The Essential Eight framework itself is well-documented. The Australian Cyber Security Centre provides detailed guidance on each mitigation strategy and maturity level. You can read it all online for free.
The challenge isn’t understanding what Essential 8 is. The challenge is:
Knowing where you actually stand today.
Do you have the controls in place? Are they configured correctly? What maturity level are you actually at—not what you assume or hope?
Determining the right target for your business. Not every organisation needs Maturity Level 3. What do your clients expect? What does your insurer require? What’s realistic given your resources?
Implementing controls without disrupting operations. Application control sounds straightforward until it blocks legitimate software your team relies on. Patching seems simple until an update breaks a critical system.
Proving your compliance to stakeholders. Your insurer wants evidence. Your client wants documentation. Your board wants assurance. How do you demonstrate what you’ve achieved?
The Challenge
The Essential Eight framework itself is well-documented. The Australian Cyber Security Centre provides detailed guidance on each mitigation strategy and maturity level. You can read it all online for free. The challenge isn't understanding what Essential 8 is. The challenge is:
Knowing where you actually stand today.
Determining the right target for your business.
Implementing controls without disrupting operations.
Proving your compliance to stakeholders.


Why Grassroots IT
We've Done It Ourselves
We Find the Right Level, Not the Highest Level
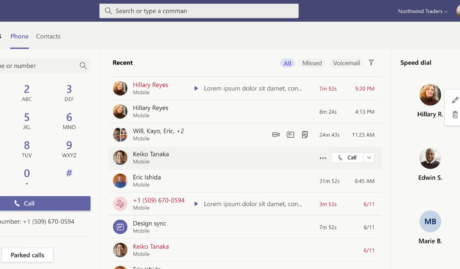
We Maximise Your Existing Microsoft Investment
Implementation That Actually Sticks
Local Team, Australian Context
What is Essential 8
The Eight Strategies
1. Application Control
2. Patch Applications
3. Configure Microsoft Office Macros
4. User Application Hardening
5. Restrict Administrative Privileges
6. Patch Operating Systems
7. Multi-Factor Authentication
8. Regular Backups
The Maturity Levels

The Maturity Levels
The ACSC defines four maturity levels (0-3), with each level representing increasing protection against more sophisticated threats:
Level 0: Weak or absent controls—you’re exposed to basic attacks.
Level 1: Basic protection against opportunistic attackers. A solid starting point for most SMEs.
Level 2: Protection against more capable, targeted attacks. Appropriate for businesses with compliance requirements or valuable data.
Level 3: Comprehensive protection against sophisticated threats. Required for high-risk industries and critical infrastructure.
Which level is right for you? That’s exactly what we help you determine. We assess your risk profile, stakeholder requirements, and resources to find the appropriate target—then build a realistic roadmap to achieve it.
Level 0:
Level 1:
We understand SME realities—limited budgets, small teams, competing priorities. Our recommendations are prioritised by risk and achievability. We tell you what matters most and what can wait, not just what’s theoretically ideal.
Microsoft Specialists
Most of our clients run Microsoft 365, and we know the platform deeply. We assess not just whether you have the right security tools, but whether they’re configured correctly—often uncovering significant gaps in environments that look fine on the surface.
No Obligation to Engage Further
Our audit is genuinely independent. You’ll receive a comprehensive report and recommendations regardless of whether you engage us for remediation. Many businesses take our findings to their existing IT provider—and that’s perfectly fine. The audit stands on its own merit.
Local Team, Real Conversations
We’re based in Brisbane and we present our findings in person (or via video if you prefer). You’ll have a real conversation about what we found—not just a document dropped in your inbox. We explain the ‘so what’ behind every finding.
How We Work
Assess Where You Are
Determine Your Target
Build a Realistic Roadmap
Implement Together
Document and Demonstrate
Maintain Your Posture
What You Get
Executive Summary:
A high-level overview suitable for sharing with leadership or your board—key findings, overall risk assessment, and priority recommendations.
Detailed Findings Report:
Comprehensive documentation of each finding with risk rating, current state, recommended state, and remediation guidance.
Prioritised Remediation Roadmap:
A practical action plan organised by priority, with estimated effort levels to help you plan resources and budget.
Framework Alignment Score:
Where relevant, your current position against Essential 8, SMB1001, or other frameworks—useful for certification planning or compliance evidence.
Presentation Session:
A face-to-face (or video) session to walk through findings, answer questions, and discuss next steps.
Ready to Get Essential 8 Right?
Whether you’re starting from scratch, responding to an insurer’s requirements, or looking to improve your existing maturity level, we can help. Book a conversation with our security team to discuss your situation and understand what working together would look like.